table of contents
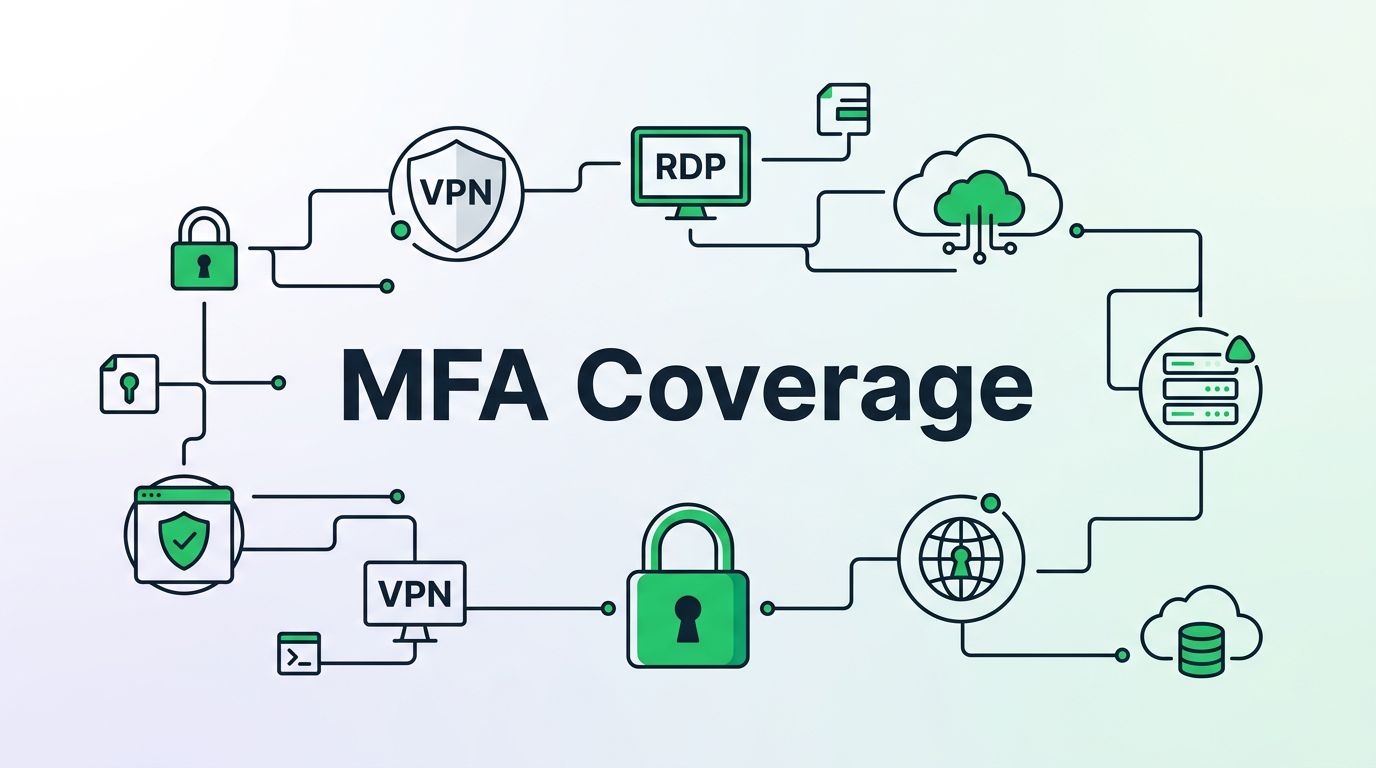
Legacy apps often look protected because MFA is turned on somewhere in the stack. That assumption breaks fast when users can still reach the app through VPN, RDP, a shared account, or an old login path.
MFA coverage validation checks every place a user or service can get in, then proves MFA or a valid compensating control is enforced there. If you only review the identity provider, you miss the paths attackers use most. You need to verify the app, the network, and the user workflow together.
Start with a complete access map
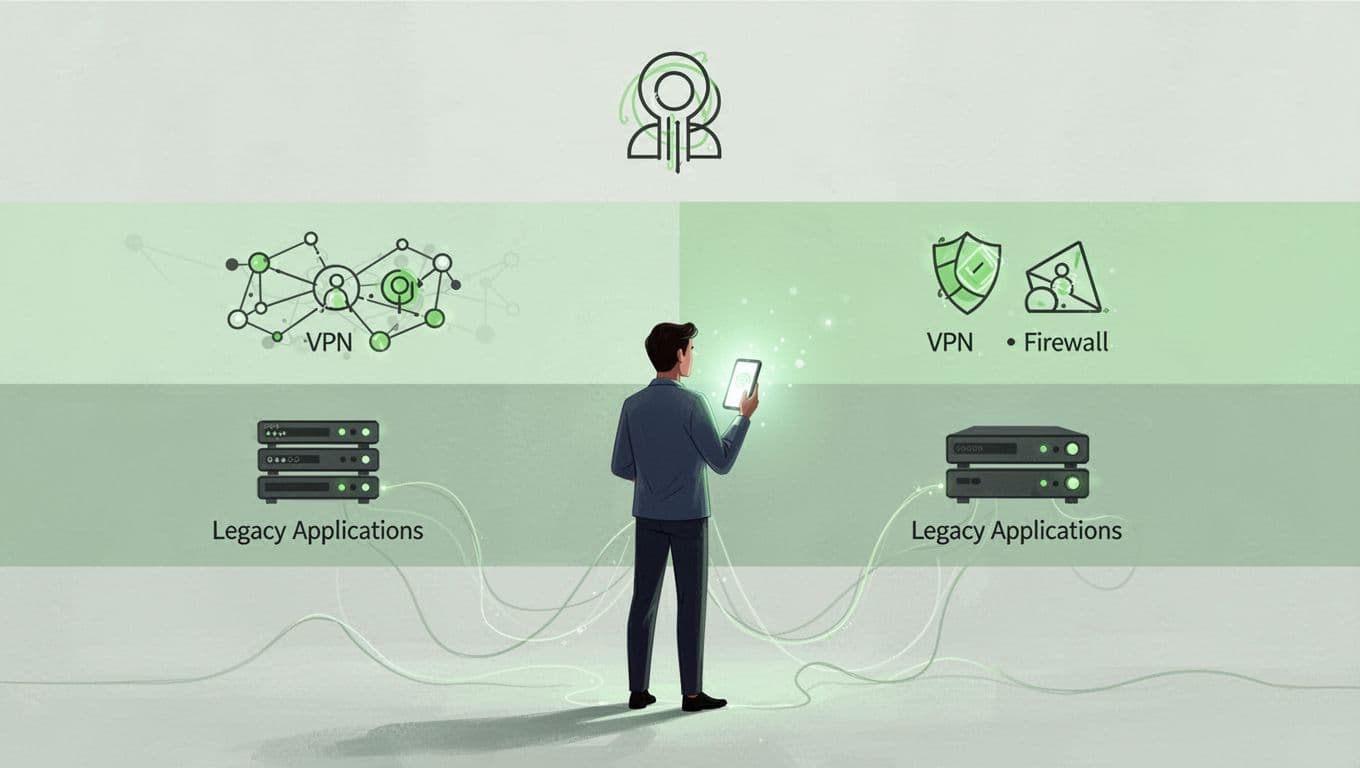
Begin by listing every route into the application, not just the main sign-in page. That means direct web access, federation, reverse proxies, VPN entry, RDP jump boxes, shared admin portals, and any basic-auth or local account path.
Legacy environments often hide useful shortcuts. Users may reach the same data through a report server, a database console, or a support tool that never touches the IdP. If that sounds familiar, identifying hidden MFA gaps becomes more than a nice-to-have.
Include service accounts too. They may not use interactive MFA, but they still need tight controls, such as certificate-based auth, network restrictions, or one-time access paths. Shared accounts need extra care, because one password can turn into many hands.
If another path reaches the same app, it needs the same control.
A clean access map gives you the scope for testing. Without it, you only prove that one door is locked.
Check enforcement at four layers, not one
MFA coverage fails when teams test only one layer. The identity provider can show a green status while the app still accepts a local login. Network access can require MFA, yet an admin can still RDP straight in. That is why validation has to follow the path end to end.
| Layer | What to prove | Common false signal |
|---|---|---|
| Identity provider | Policy applies to all users, admins, and privileged groups | Per-user MFA flags or old registration methods still in use |
| Network and remote access | VPN, RDP, bastions, and proxies require challenge before session | MFA happens only after the tunnel opens |
| Application layer | SSO, federation, or proxy rules block direct access | A direct URL or basic-auth endpoint still works |
| User workflow | Enrollment, step-up, and re-auth happen when risk changes | One-time enrollment with long-lived sessions |
For older apps that do not support SAML or OIDC, legacy app SSO and MFA guidance can help frame the options. In 2026, the best programs also move away from stale per-user MFA settings and toward unified auth method policies, phishing-resistant factors for admins, and step-up checks for risky actions.
The real question is simple. Can a user get to the same data without proving the same level of trust? If the answer is yes, the control is incomplete.
Run tests that follow real users and real attackers
Validation works best when it mirrors real behavior. Use fresh sessions, different devices, and multiple entry points. Then compare what the user sees with what the logs show.
Test scenarios should include:
- A direct browser login to the legacy app, with no cached session.
- A federated login through the IdP, followed by a direct app URL.
- VPN access, then access from an RDP or jump-host path.
- A shared admin account, with proof that individual approval still applies.
- A service account, with proof it cannot be used interactively.
- A step-up event, such as a sensitive action, a new device, or a new location.
Each test should tell you whether MFA truly happens before access, or only during enrollment. It should also show where the flow breaks, such as a fallback local login, a remembered-device bypass, or a proxy that accepts traffic without checking the user.

When testing older systems, record timestamps, source IPs, protocol type, and the exact path used. Those details matter when a reviewer needs to prove that the control blocked a real bypass, not just a happy-path login.
Collect evidence that stands up in an audit
Audit evidence should prove enforcement, not enrollment.
For every critical app, keep proof that shows the control at work. That evidence usually includes IdP policy exports, VPN or RDP logs, app or gateway authentication logs, and screenshots or recordings of the challenge flow. If the app is exempt, keep the exception, the owner, and the expiry date.
A strong evidence pack also shows how you handled weak spots. That may include compensating controls for service accounts, network segmentation for old systems, and break-glass procedures for emergency access. For a good reference point on extending protection across hybrid paths, see the guide to closing legacy authentication gaps.
Watch for false MFA assumptions. Common ones include MFA only on the main portal, “remember this device” set too long, direct basic-auth endpoints still alive, and shared accounts that bypass user-level proof. Another red flag is a legacy app that sits behind SSO while local admin access remains untouched.
Keep legacy coverage under review
Legacy applications change slowly, but their access paths do not. A new VPN rule, a proxy update, or a forgotten admin account can reopen a gap that looked closed last quarter.
The safest pattern is repeatable validation. Map the routes, test each one, collect proof, and retire exceptions with a date attached. That is how MFA coverage validation becomes a control you can trust, not a box you checked once and forgot.
If your team needs a second set of eyes on legacy access paths, Book a Discovery Call with Bud Consulting.