table of contents
You’re a security leader facing a flood of vulnerability reports. AI tools crank out low-quality submissions, and your team struggles to keep up. A skilled bug bounty coordinator can turn that chaos into actionable security wins. This guide shows you how to spot and hire one who fits your needs.
Bug bounty programs save companies millions by crowdsourcing fixes before attacks hit. Yet, poor coordination leads to burnout, delays, and missed threats. You need someone who bridges hackers and your engineers. Let’s break down the role and your hiring steps.
What a Bug Bounty Coordinator Does Daily
A bug bounty coordinator manages the flow of reports from ethical hackers. They triage submissions, validate issues, and push fixes through your pipeline. This person owns the program from intake to payout.
Most days start with inbox checks. Coordinators scan platforms for new reports, assign severity, and duplicate-check against known issues. They chat with researchers to clarify details without giving away fixes. Then, they escalate critical bugs to devs.

Expect them to update program scopes too. As your attack surface grows with AI apps and APIs, they adjust rules to focus hunters on high-value areas. They track metrics like mean time to triage, which top programs keep under 48 hours.
Coordinators also handle disclosures. They coordinate public announcements after patches land, following rules like 90-day timelines. This builds trust with the community. In 2026, with AI noise overwhelming platforms, their role matters more than ever.
How This Role Differs from Similar Security Jobs
Many mix up bug bounty coordinators with vulnerability managers or AppSec engineers. Each has distinct focus areas.
Vulnerability managers scan for known issues using tools like Nessus. They patch systems and track compliance across your fleet. A coordinator, however, deals with unknown zero-days from external hunters. They don’t scan; they react to crowdsourced finds.
AppSec pros embed security in code reviews and CI/CD. They prevent bugs during development. Coordinators come after, validating live reports and mediating between hunters and your AppSec team.
SOC analysts watch for active exploits in logs. Coordinators prevent exploits by fixing them first through bounties. Security program managers oversee broad strategies like training. Coordinators execute the bounty piece with hands-on triage.
| Role | Focus | Tools/Processes | Key Output |
|---|---|---|---|
| Bug Bounty Coordinator | External reports, researcher liaison | Platforms like Bugcrowd, triage dashboards | Validated bugs, payouts, disclosures |
| Vulnerability Manager | Known CVEs, scanning | Nessus, Qualys | Patched systems, compliance reports |
| AppSec Engineer | Code security | SAST/DAST, threat modeling | Secure pipelines, fewer dev bugs |
| SOC Analyst | Incident response | SIEM, alerts | Contained breaches |
This table highlights why you need a specialist. A coordinator turns bounty programs into force multipliers, unlike internal-only roles. For details on coordinator duties, check this job posting from Ubisoft.
Key Skills Every Bug Bounty Coordinator Needs
Top coordinators blend technical chops with people skills. They read reports like a pentester but communicate like a project manager.
Start with security basics. They know OWASP Top 10, MITRE ATT&CK, and common flaws like IDOR or prompt injection in AI apps. Hands-on experience hunting or triaging helps them spot valid claims fast.
Communication tops the list. They explain bugs to devs without jargon and negotiate with frustrated researchers. Expect stories of de-escalating disputes over duplicate reports.

Platform savvy is non-negotiable. Familiarity with Intigriti or HackerOne lets them optimize scopes and rules. They enforce policies, like out-of-scope rejections, to cut noise.
Stakeholder management rounds it out. They align product leads, legal, and execs on risks. In 2026 trends, they handle AI-generated report surges by setting quality filters.
Look for 2-5 years in security, plus bug bounty participation. Certs like OSCP add credibility, but real reports triaged matter more.
Triage Workflows That Coordinators Master
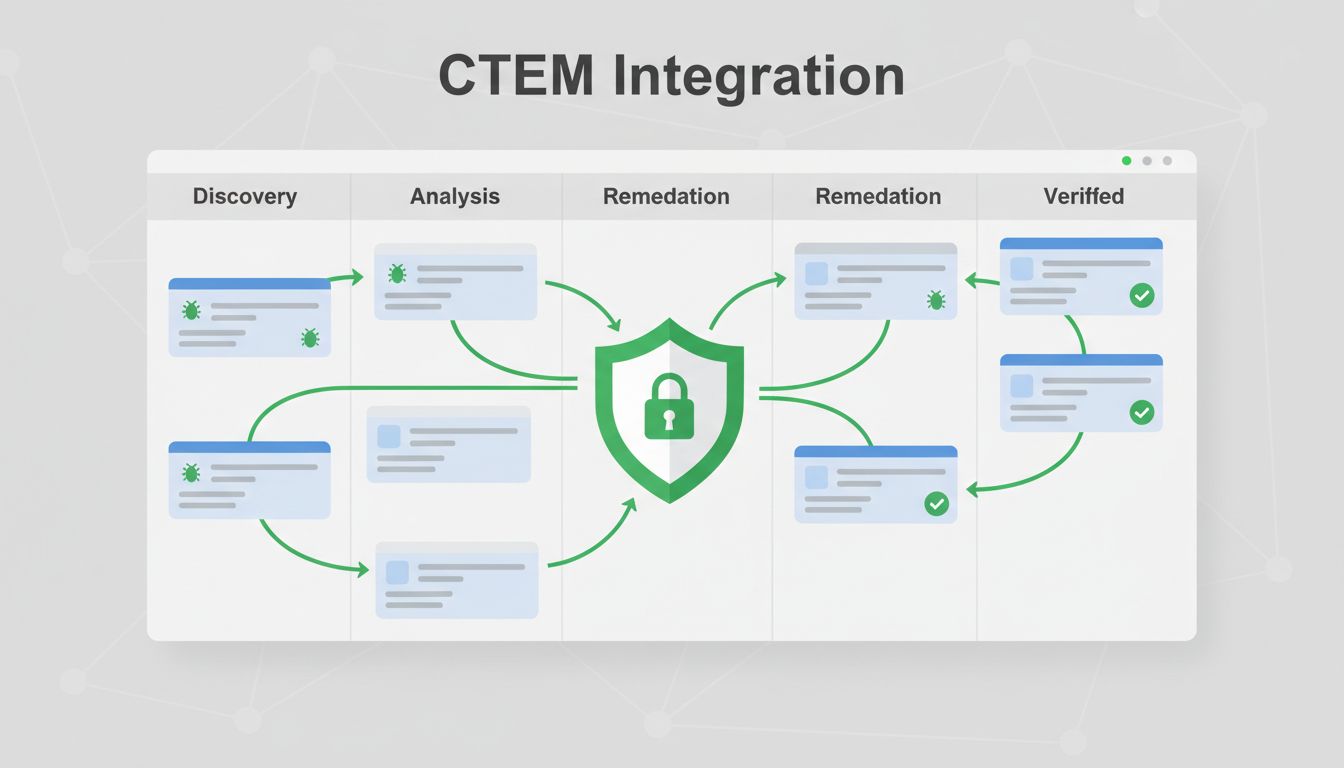
Efficient triage separates great coordinators from average ones. They prioritize to focus teams on real threats.
First, they assess severity using CVSS scores or business impact. A login bypass trumps a low-info leak. They validate with PoCs, retesting steps in controlled envs.
Workflows often use shared dashboards. Coordinators assign tickets, set SLAs, and follow up. They dedupe against internal scans, rejecting AI-spammed duplicates common in 2026.

Disclosure handling follows. They draft coordinated releases, notifying researchers first. Legal awareness prevents slip-ups, like avoiding NDA violations.
Platform coordination shines here. They sync with Bugcrowd or YesWeHack for seamless intake. Policy enforcement keeps programs fair, banning bad actors.
Here’s a quick checklist for strong triage:
- Intake: Auto-filters + manual review within 24 hours.
- Validate: Reproduce, score, dedupe.
- Escalate: Notify teams with clear steps.
- Close loop: Payout, disclose, lessons learned.
Coordinators who nail this reduce MTTR to days, not weeks.
Crafting a Smart Hiring Process
Build your job req around outcomes. List must-haves: triage experience, platform use, comms samples.
Post on security boards and platforms like LinkedIn. Highlight your program’s scope to attract hunters-turned-coordinators. Budget for remote US talent; most roles allow it.
Screen resumes for bounty platforms or pentest reports. Phone chats test researcher empathy: “How’d you handle a duplicate claim?”
Assess culture fit early. They join cross-functional teams, so probe collaboration stories.
Salary benchmarks help. In 2026, expect $100,000 to $115,000 base in the US, per Glassdoor data on similar roles. Add equity for startups. Top earners hit $160,000 with experience.
Tailor comp to trends. Offer bonuses tied to KPIs like valid report volume.
If gaps persist, Book a Discovery Call with Bud Consulting for vetted candidates.
Interview Questions to Spot Top Coordinators
Interviews reveal true fit. Use behavioral probes tied to responsibilities.
Ask: “Walk us through triaging a high-severity report.” Listen for validation steps, stakeholder loops.
Probe comms: “Describe calming an upset researcher over a rejected bounty.” Good answers show empathy plus policy firmness.
Test metrics knowledge: “What KPIs track program health?” Expect MTTR, fix rates, researcher retention.

For legal: “How do you handle disclosure timelines?” They should cite 90-day standards, vendor coordination.
Role-play a platform scenario: “Our Bugcrowd scope excludes APIs; a hunter submits one. Your response?” Firm, polite rejection wins.
End with: “How would you adapt our program to 2026 AI report floods?” Seek filters, training ideas.
Follow up with a take-home: Triage sample reports. Grade on clarity, speed, accuracy.
Metrics, KPIs, and Legal Essentials
Coordinators drive measurable security. Track these KPIs:
- MTTR: Under 7 days for criticals.
- Fix Rate: Above 1.2 (fixes exceed finds).
- Valid Report %: 20-30% post-triage.
- Researcher Retention: Repeat hunters signal success.
Dashboards visualize trends. Coordinators report quarterly to justify budgets.
Legal smarts protect you. They know safe harbor laws, like US CISA guidelines, and platform terms. Compliance covers GDPR disclosures too.
In 2026, with Web3 and gov programs rising, they adapt metrics to new bounties, like Immunefi’s crypto highs.
Key Takeaways for Your Hire
Hire a bug bounty coordinator who turns reports into defenses. Focus on triage pros with researcher rapport. Differentiate from vuln managers; this role crowdsources your edge.
You’ll cut risks and build community trust. Start screening today; the right hire pays off fast.
Strong programs thrive amid AI noise. Your team gains fixes from global talent. What holds your program back? Fix it with the right coordinator.