table of contents
Your first weeks in a security leadership role shape how the team sees you, and how the business trusts you. If you spend that time chasing status updates and tool access, you lose momentum before you start.
A strong security leadership onboarding plan helps you learn the team, understand the risk, and set clear expectations fast. It also keeps you from making changes before you know what is working.
The goal is simple: build trust, reduce noise, and show that you can lead with facts. Start with people and risk, then turn that into a clear 90 day rhythm.
Start with people, not policies
Your first job is to understand the team as it really works. Spend time with each direct report, ask how they spend their day, and listen for friction points. A policy can tell you what should happen, but the team will show you what happens when alerts spike or someone is out sick.
A general manager onboarding checklist helps with the basics, but security leadership needs more. You need to know who owns incident response, who approves access changes, and where escalations stall.
Use these questions in your first one on ones:
- What work gets ignored when things get busy?
- Which risks come up again and again?
- What do you want leadership to understand about this team?
- Which tool or process wastes the most time?
- Where would a delay cause real business pain?
Make time for peers too. Talk with IT, infrastructure, legal, HR, finance, and key product leaders. Those conversations show you where security depends on other teams, and where other teams depend on security.
Trust comes faster when you ask clear questions, then act on what you hear.

Map the real risk in the first two weeks
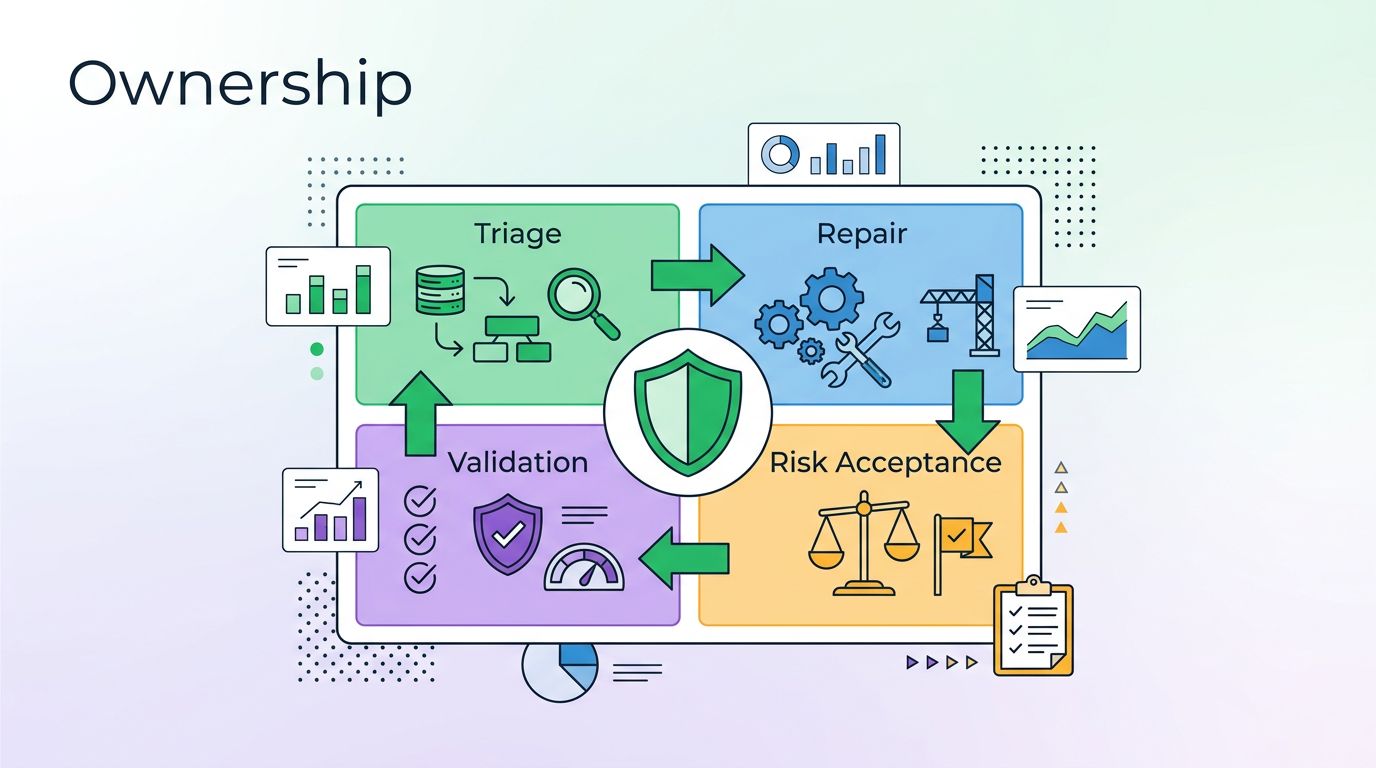
Once you understand the people, move to the risk picture. Read the last few incident reports, check open vulnerabilities, review policy exceptions, and identify the systems that matter most to the business. You are looking for the problems that could hurt operations, revenue, or trust.
In 2026, that usually means cloud access, identity sprawl, third-party exposure, and stale remediation work. A current CISO onboarding checklist can help you spot what a rushed handoff might miss. It can also remind you to verify the basics, not just the dashboard.
Focus on these items early:
- Top incidents from the last 90 days
- Open risks with no clear owner
- Privileged access and MFA coverage
- Vendor and partner access paths
- Audit deadlines and control gaps
- Security tools that no one fully owns
If you inherit a large program, compare it with a first 90 day security leadership plan. The structure helps, even if your priorities end up different. For a broader view of what many leaders are watching this year, CISO priorities for 2026 gives useful context on business risk, third parties, and executive pressure.

Turn the first 90 days into a simple operating rhythm
A 30, 60, 90 day plan keeps you from reacting to every alert. It also gives your team a steady pace while you learn how the organization makes decisions.
Here is a simple way to structure it:
| Timeframe | Main focus | Proof you are on track |
|---|---|---|
| 0 to 30 days | Learn and verify | Team map, risk list, incident flow, stakeholder list |
| 31 to 60 days | Stabilize | Top fixes, clear owners, better escalation, fewer blind spots |
| 61 to 90 days | Align and report | Prioritized roadmap, metrics, budget asks, executive update |
Use that plan to set a working cadence. Weekly one on ones keep you close to the team. Biweekly risk reviews help you track decisions. Monthly executive updates keep leadership informed without drowning them in detail.
Your 90 day checklist should also cover:
- One page goals for the team
- A current view of service health and incident trends
- A list of decisions that need senior approval
- A draft roadmap with owners and dates
- A short list of quick wins you can land early

Speak to executives in business terms
Security leaders do not win trust by sounding technical. They win trust by making risk clear and useful. Executives want to know what is exposed, what it could cost, and what choice they need to make.
Keep your updates short. Lead with the business impact, then give the security detail only when it supports the decision. If a fix needs budget, say so. If a policy needs an owner, name the gap. If a control needs time, explain the tradeoff.
Good questions for leadership meetings include:
- Which risk would hurt the business most this quarter?
- What decision is stuck because ownership is unclear?
- Which control gap needs a sponsor outside security?
- What would you like to see in my next update?
That style of communication changes how people respond to you. It turns security from a report into a partner.
Build a handoff you can actually run
The best onboarding plans do more than help you survive the first month. They give you a repeatable way to lead, measure, and adjust. Start with people, map the risk, set the cadence, then speak in business terms.
If your new role comes with a messy handoff or a fast-moving team, Book a Discovery Call with Bud Consulting to shape a practical first 90 days plan. A strong start in security is built on clarity, not guesswork.