table of contents
CTEM works only when findings move to the right people fast. If a team can spot exposure but can’t assign it cleanly, the backlog grows and risk stays put.
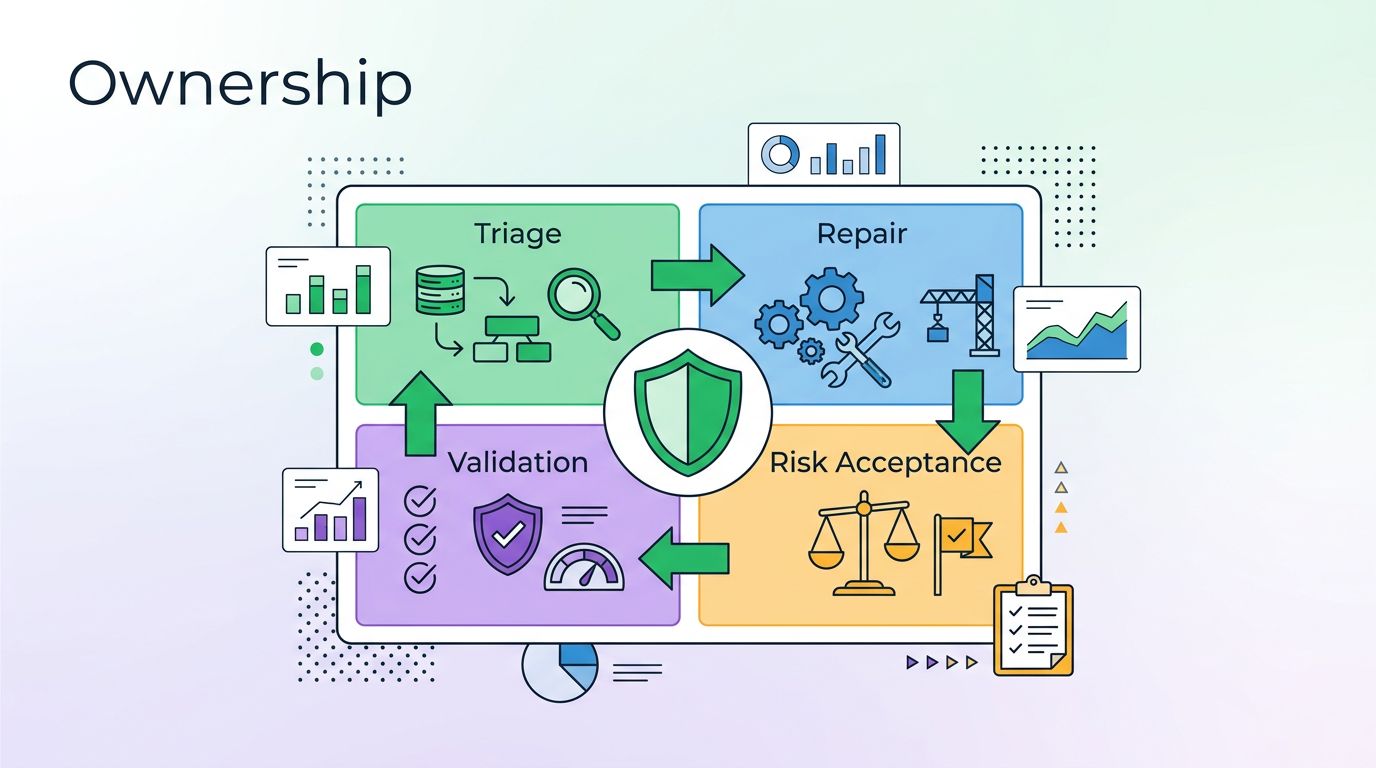
A strong CTEM ownership matrix solves that problem. It turns vague follow-up into a clear path for triage, repair, validation, and risk acceptance. That matters because CTEM is about reducing real exposure, not just collecting alerts, as explained in Astelia’s CTEM overview.
A finding without a clear owner will sit in backlog until someone feels pain.
Why ownership breaks CTEM programs
Most security teams already know what is wrong. The harder part is deciding who owns the next move. That gap slows remediation more than most tools do.
In CTEM, ownership is more than a ticket assignee. It is a working agreement that tells everyone who finds the issue, who fixes it, who checks the fix, and who signs off on exceptions. That structure matters because exposures change fast, and teams need fewer handoffs, not more.
A well-run matrix also cuts debate. Instead of arguing over whether an IAM problem belongs to cloud, identity, or security, the team follows a pre-set rule. The result is faster routing and less drift between teams.
The pressure is real. The 2026 CTEM divide research shows a sharp gap between teams that treat CTEM as an operating model and teams that treat it as a report. Ownership is one of the main reasons that gap keeps widening.
The four roles that make the matrix work
A lot of teams mix up ownership terms. That creates confusion during triage. A clean matrix separates the roles so each one has a different job.

The matrix below shows a practical split for common CTEM findings.
| Finding type | Finding owner | Remediation owner | Validation owner | Exception approver |
|---|---|---|---|---|
| IAM issue | Identity security or CTEM triage team | IAM or PAM team | Security validation team | App owner or security risk owner |
| Exposed service | CTEM triage team | Cloud or network operations | Security validation team | Service owner or platform leader |
| Misconfiguration | Cloud security or platform security | Cloud platform or DevOps | Security validation team | System owner |
| Unpatched asset | Vulnerability management | Endpoint or infrastructure team | Vulnerability management | IT owner or risk owner |
| Application flaw | AppSec or CTEM triage team | Engineering team | AppSec validation | Product owner |
| Third-party exposure | Vendor risk or CTEM triage team | Vendor manager or business owner | Security team | Business owner or CISO delegate |
The key point is simple. The finding owner manages the ticket and the handoff. The remediation owner changes the system. The validation owner confirms the exposure is gone. The exception approver accepts the risk when a fix cannot happen yet.
That split keeps teams from hiding behind one another. It also helps leaders see where work stalls.
How the matrix improves prioritization and coordination
A good matrix does more than assign names. It helps you rank work based on who can move fastest and where risk is highest.
For example, an internet-facing exposed service with active exploitation evidence should move ahead of a low-risk internal misconfig. An IAM issue with broad privilege gets higher priority than a cosmetic policy drift. An unpatched asset tied to a critical business service deserves faster handling than the same issue on a lab box.
The matrix makes those calls easier because it ties each finding to a real team. That means the security team can sort by ownership and urgency at the same time. It also gives engineering and infrastructure teams a cleaner view of what they need to act on.

That shared view matters when remediation touches several groups. Cloud teams often fix exposure paths. App teams fix code and dependencies. IAM teams fix access and role design. Security then validates the result and closes the loop.
The CTEM ownership matrix also reduces the “who owns this?” meetings that drain time. If everyone knows the rules, the team spends more time fixing and less time routing.
How to build the matrix without making it heavy
Start with the findings you see most often. Do not try to model every edge case on day one. A narrow list works better, because teams will use it.
- Define your top finding classes, such as IAM, exposed services, misconfigurations, unpatched assets, application flaws, and third-party exposure.
- Assign one primary finding owner for each class. Keep it consistent across business units.
- Map each finding class to one remediation owner and one validation owner.
- Set an exception path for cases that need risk acceptance, and name the approver.
- Write routing rules in plain language, then publish them where teams already work.
If you already use shared exposure terms, align the matrix with CTEM controls and identifiers. That helps avoid duplicate labels and mixed handoffs.
Keep the rules short. If a rule needs a paragraph, it’s too complex. The best matrices fit on one page and still answer the hard questions.
You can also tie the matrix to SLAs. For example, critical internet-facing findings may need same-week triage and a fast validation check. Lower-risk issues can follow normal sprint timing. The point is to match response speed to exposure level.
If the routing still feels fuzzy, use a workshop with security, cloud, IAM, AppSec, and engineering leads. A short working session will reveal most ownership gaps fast. If you want help setting that up, Book a Discovery Call with Bud Consulting.
The best CTEM programs do one thing well. They turn findings into named action, then prove the risk is gone. When ownership is clear, remediation gets faster and accountability stops being a debate.