table of contents
Security awareness RFPs fail when they read like feature wish lists. In 2026, that gets expensive fast, because phishing, deepfakes, and simple mistakes still drive most breaches.
A good vendor should help change behavior, fit your stack, and give audit-ready evidence. If your security awareness RFP does not ask for that, vendors will fill the gaps with marketing language.
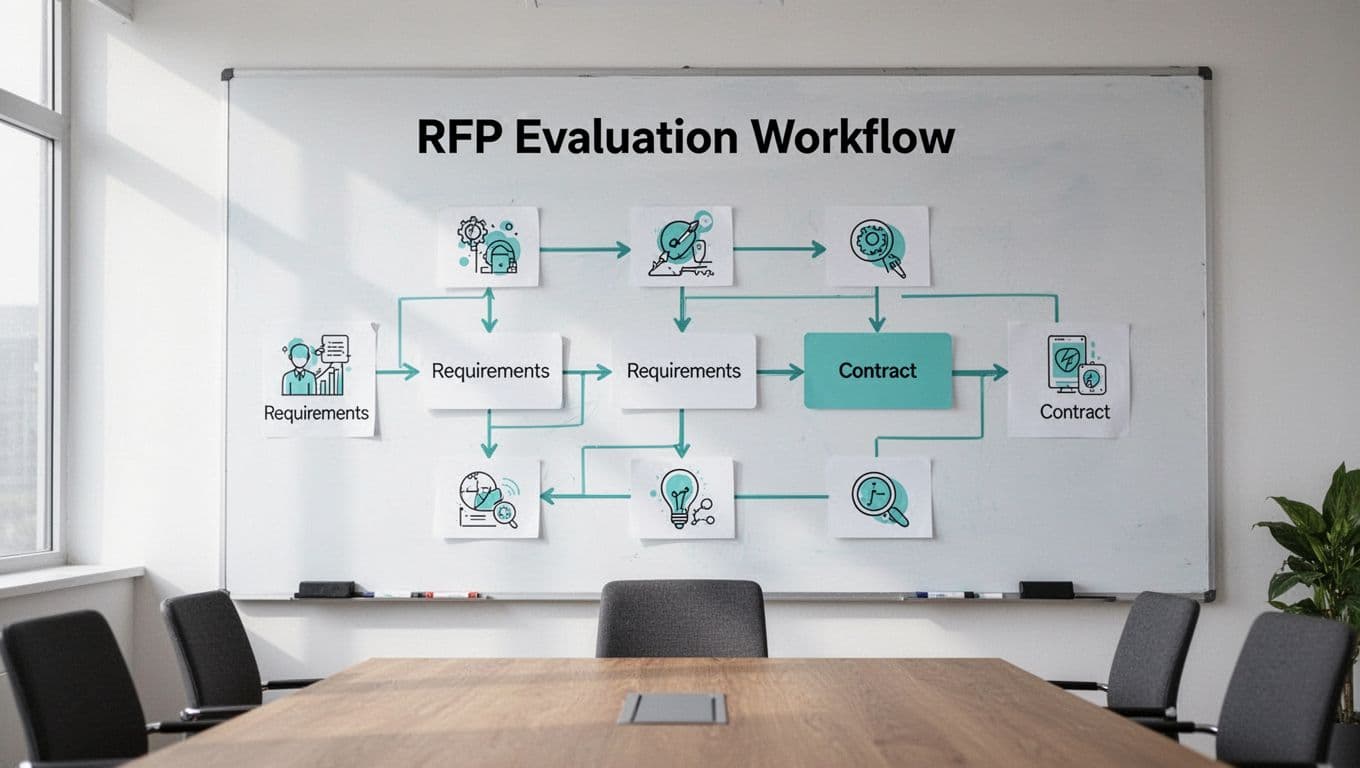
Use the framework below to write a cleaner, tougher RFP.
Why your RFP needs sharper questions in 2026
People still create most breach paths, and attackers now use AI to make scams feel familiar. That means your RFP has to test more than content libraries. It should show how a vendor handles simulations, reporting, admin load, and proof of behavior change.
Completion rates matter, but they only tell part of the story. You need evidence that employees click less, report more, and make fewer risky choices over time. For a broader planning lens, TechTarget’s guide on how to build a cybersecurity RFP is a useful companion.
Ask vendors for proof, not promises.

Copy-ready security awareness RFP template
Use this structure as a starting point, then tune it for your environment. The wording is tight on purpose, so vendor replies are easier to compare.
| RFP section | Sample requirement language |
|---|---|
| Company profile | “Describe support for [headcount], [regions], [languages], and regulated data.” |
| Content quality | “Provide role-based, current content with short modules and behavior nudges.” |
| Phishing simulations | “Support email, SMS, voice, QR, and deepfake simulations.” |
| Reporting and analytics | “Show completion, click rates, risk trends, and audit-ready exports.” |
| LMS and SSO integrations | “Integrate with our SSO, LMS, HRIS, and SCIM tools.” |
| Automation | “Offer auto-enrollment, triggered campaigns, reminders, and API access.” |
| Localization and accessibility | “Support required languages and meet WCAG 2.1 AA or equivalent.” |
| Data privacy and compliance | “State retention, hosting region, subprocessors, encryption, and DPA support.” |
| Customer success and implementation | “Provide a named lead, launch plan, training, and review meetings.” |
| Pricing model | “Disclose per-user, tiered, and add-on costs, plus implementation fees.” |
| Contract and SLA | “Include uptime targets, support hours, response times, exports, and exit help.” |
Tailor the scope to your company size, risk profile, and regulatory environment. A 200-person SaaS firm will not need the same depth as a global bank. If you want a second benchmark, this buyer’s guide to security awareness training can help you compare answers without getting lost in feature names.
How to judge vendor replies without getting lost in features
Strong answers show evidence. Ask each finalist for one sample report, one live admin walk-through, and one reference from a similar company.
Use those asks to test the details that matter most.
- A sample report should show trends by team, language, and risk level.
- A demo should show how campaigns are launched, edited, and paused.
- A reference call should cover support speed, not just rollout success.
- A pricing sheet should spell out add-ons, renewal jumps, and exit help.
That last point matters more than many buyers expect. A vendor can look cheap up front and still become costly later. Hidden services, usage caps, and slow support usually show up in the second contract cycle, not the first.
Weighted scorecard for your shortlist
Score each vendor from 1 to 5, then multiply by the weight below. Shift the weights if your company has stronger privacy rules or a global workforce.
| Criterion | Weight | What good looks like |
|---|---|---|
| Content quality | 12 | Fresh, role-based, and easy to update. |
| Phishing simulations | 15 | Realistic, multi-channel, and easy to tune. |
| Reporting and analytics | 10 | Clear trends, audit exports, and manager views. |
| LMS and SSO integrations | 10 | Clean setup, low admin effort, no workarounds. |
| Automation | 10 | Triggers, reminders, and policy-based campaigns. |
| Localization and accessibility | 8 | Language support, captions, and usable design. |
| Privacy and compliance | 15 | Clear data handling, retention, and security controls. |
| Customer success and implementation | 10 | Strong onboarding, named support, and useful reviews. |
| Pricing, SLAs, and exit terms | 10 | Transparent cost, service levels, and clean offboarding. |
If you work in healthcare, finance, or the public sector, push more weight into privacy, compliance, and logging. If your workforce is spread across regions, move more weight to localization and accessibility.
Tighten the final review before you issue it
Trim anything that does not help you compare vendors. Long open-ended questions slow the process and hide weak answers. Set response formats, due dates, and demo expectations before the RFP goes out.
If your team wants help shaping the scope or pressure-testing the scoring model, Book a Discovery Call with Bud Consulting.
A strong security awareness RFP asks vendors to show how they change behavior, not how big their library is. It also forces the commercial details into the open, which saves time later.
Write for the risk you have today, not the program you hope to have next year. That keeps the RFP grounded and the vendor list honest.