table of contents
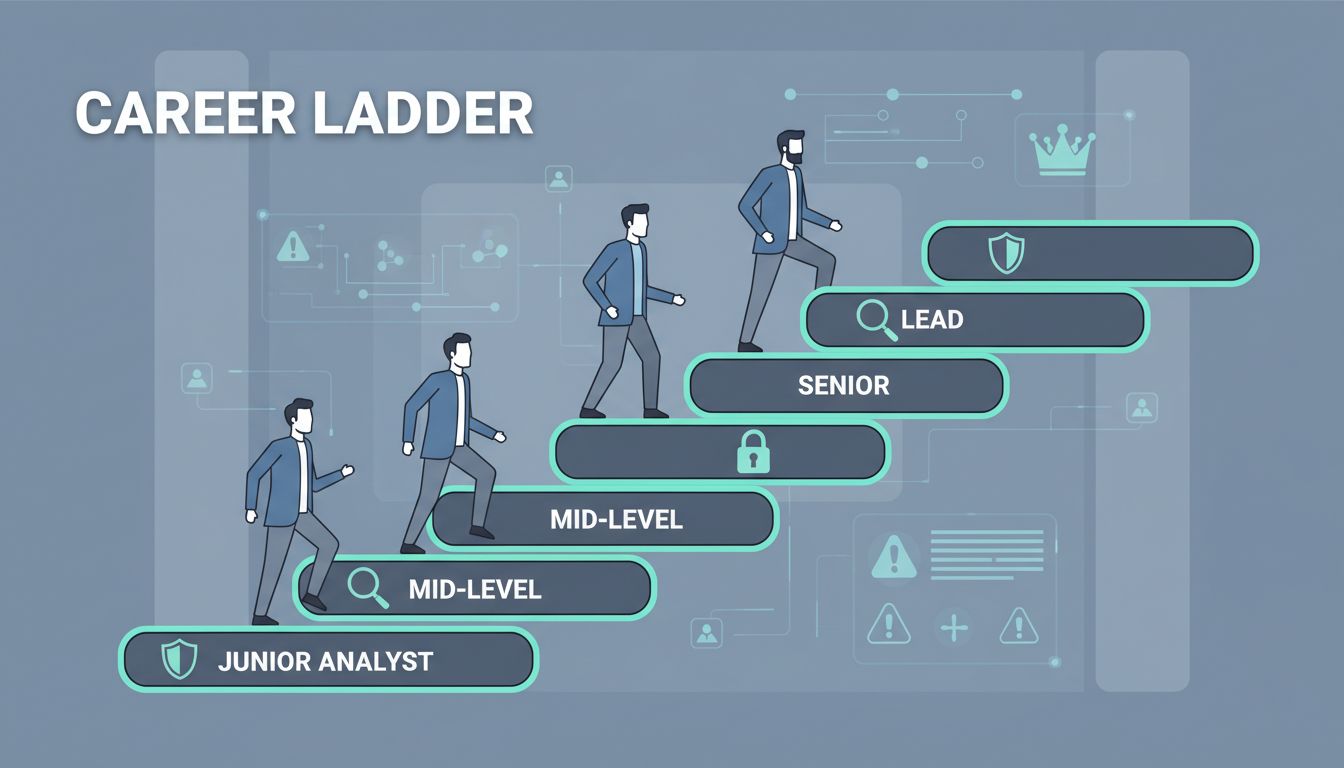
Junior analysts often join your SOC with energy but little direction. They triage alerts and learn tools, yet many stall without a clear path up. You see burnout rise as they wonder what’s next.
A solid security career ladder fixes that. It gives them milestones, keeps talent in house, and builds a stronger team. This guide shows you how to create one step by step.
Start by looking at your team’s needs. Then map roles, skills, and promotions. Your analysts will thank you with better retention and sharper threat detection.
Assess Your Team’s Needs First
Look at turnover rates in your SOC. Do junior analysts leave after a year? High churn costs time and money in 2026’s tight talent market.
Talk to your team. Ask what frustrates them most. Common issues include vague feedback and no promotion roadmap. One SOC manager found 40% of juniors felt stuck after six months.
Gather data on current skills too. Review incident reports. Spot gaps like weak scripting or slow triage times. This baseline shapes your ladder.
Set goals for the framework. Aim for 18-24 months per level, based on SOC analyst career paths. Match it to your org size. Small teams might combine levels; larger ones add branches.
Document everything. Share a one-page summary with leadership. Get buy-in early. This prevents roadblocks later.
Map Out Role Levels
Define four core levels: Junior Analyst, Analyst, Senior Analyst, and Lead Analyst. Each builds on the last. Juniors handle basics; leads mentor and innovate.
Juniors focus on alert triage and escalation. Analysts dive into investigations. Seniors hunt threats and tune detections. Leads own processes and guide teams.
Expect 1-2 years at junior level, 2 years each after that. Adjust for talent. Here’s a quick view:
| Role | Focus Areas | Years Typical |
|---|---|---|
| Junior Analyst | Triage, basic response | 0-2 |
| Analyst | Investigations, reporting | 2-4 |
| Senior Analyst | Threat hunting, automation | 4-6 |
| Lead Analyst | Mentoring, process ownership | 6+ |
This table draws from common SOC tiers. It keeps progression logical. Analysts see the climb ahead.

Visual ladders like this help during onboarding. Post it in your SOC wiki. Teams grasp the path fast.
Define Measurable Competencies
Skills drive promotions, not just time served. Build a matrix with categories like threat detection, incident response, and tool proficiency.
Rate levels from basic to expert. Juniors need SIEM basics; seniors write custom rules. Make it objective.
- Threat Detection: Juniors spot alerts; seniors build YARA rules.
- Incident Response: Analysts contain breaches; leads run tabletop exercises.
- Tools Proficiency: Start with Splunk queries; advance to EDR scripting.
- Soft Skills: All levels communicate findings; leads present to execs.
Use a simple scale: Aware, Proficient, Advanced, Expert. Track progress quarterly.
For a full example, check this cybersecurity job leveling matrix.
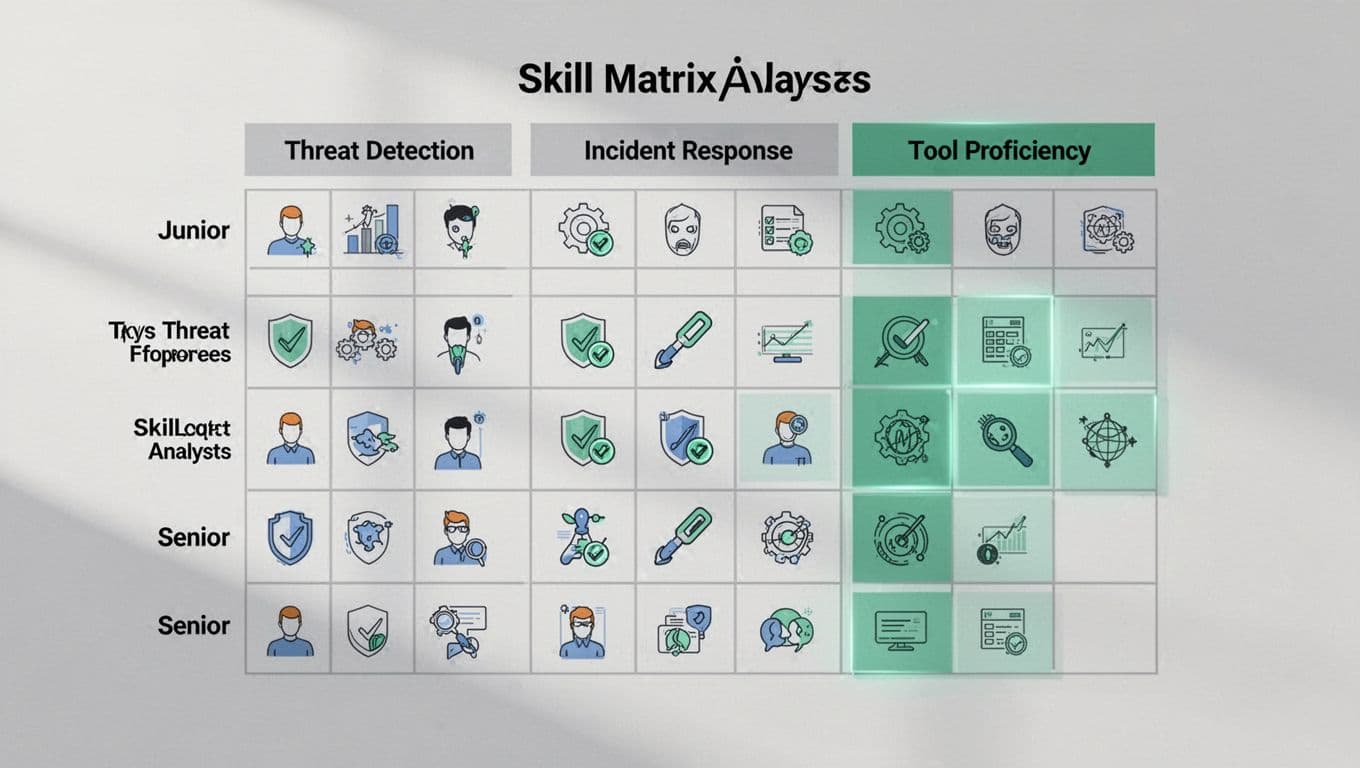
This grid clarifies expectations. Tie it to performance reviews. Analysts know exactly what to target.
Set Clear Promotion Criteria
Promotions need proof, not promises. List requirements per level.
For junior to analyst:
- Handle 80% of alerts independently.
- Complete two certifications like Security+ or CySA+.
- Document five full investigations.
Analyst to senior:
- Lead three incidents end-to-end.
- Automate one daily task.
- Mentor a junior for one quarter.
Use rubrics. Score on a 1-5 scale across competencies. Require 4+ average plus one standout project.
Review twice yearly. Involve peers for fairness. Share tier progression tips to guide them.
Track metrics like mean time to respond. Better numbers show readiness. Celebrate promotions team-wide.
Best Practices for Managers and Teams
Managers make ladders work. Hold monthly 1:1s. Review matrices and set one goal per skill gap.
Assign stretch projects. Pair juniors with seniors on hunts. Rotate shifts for broad exposure.
Train on feedback. Use SBI model: Situation, Behavior, Impact. “In last week’s breach, your root cause analysis cut response time by 20%.”
Foster culture. Run ladder workshops. Share success stories.

These talks build trust. Track adoption with surveys. Adjust based on input.
If implementation feels overwhelming, Book a Discovery Call with Bud Consulting. They help tailor frameworks.
Conclusion
A security career ladder turns junior analysts into leads. It cuts churn, sharpens skills, and strengthens your SOC.
Focus on clear roles, matrices, and criteria first. Managers execute with regular check-ins. Your team climbs faster as a result.
Start small. Pilot with juniors. Scale what works. Retention improves right away.