table of contents
Hybrid cloud setups now power most enterprises, but they expose you to breaches from misconfigurations and visibility gaps. In 2026, 80% of data breaches tie back to cloud-linked issues, and the CSPM market hits $3.77 billion as teams scramble for better protection. You mix on-premises servers with AWS or Azure, so security can’t stay siloed.
Pure cloud security focuses on APIs and shared responsibility. On-premises relies on firewalls and VLANs. Hybrid demands you bridge both worlds. This article shows you how to create a unified hybrid cloud security framework that aligns policies, boosts visibility, and enforces controls everywhere. Start with the challenges, then build step by step.
Understand Hybrid Cloud Security Challenges
Hybrid environments blend on-premises data centers with public clouds. Data flows freely, but risks multiply. Attackers exploit gaps between systems.
Common threats include inconsistent IAM, where users gain excess privileges across platforms. Old accounts linger, and logs don’t match. Misconfigured networks let threats move laterally. Shadow IT adds unmonitored tools. For details on these issues, check TechTarget’s guide to hybrid cloud security challenges.
Fragmented visibility creates blind spots. On-premises tools miss cloud-native logs. Policy drift happens as configs change over time. In 2026, these problems drive most incidents, per recent reports.

Data in transit faces leaks without end-to-end encryption. Compliance like GDPR adds pressure across jurisdictions. Unlike single-cloud setups, hybrid lacks native unity. You need tools that span environments.
Zero-trust helps here. Verify every access, no matter the origin. Still, manual checks fail at scale. Automation becomes key.
Key Components of a Hybrid Cloud Security Framework
A solid framework rests on three layers: policy, visibility, and controls. Policy sets rules that apply everywhere. Visibility maps assets and threats. Controls enforce and automate fixes.
Start with unified policy management. Define standards once, then push to on-premises and cloud. Use frameworks like NIST CSF for guidance, as Sprinto outlines in their hybrid security post.
Visibility requires tools like CSPM for posture scans and CNAPP for runtime protection. SIEM aggregates logs from all sources. This gives one dashboard view.
Controls layer in IAM for least-privilege access, SOAR for response workflows, and zero-trust gateways. IAM federates identities across domains.
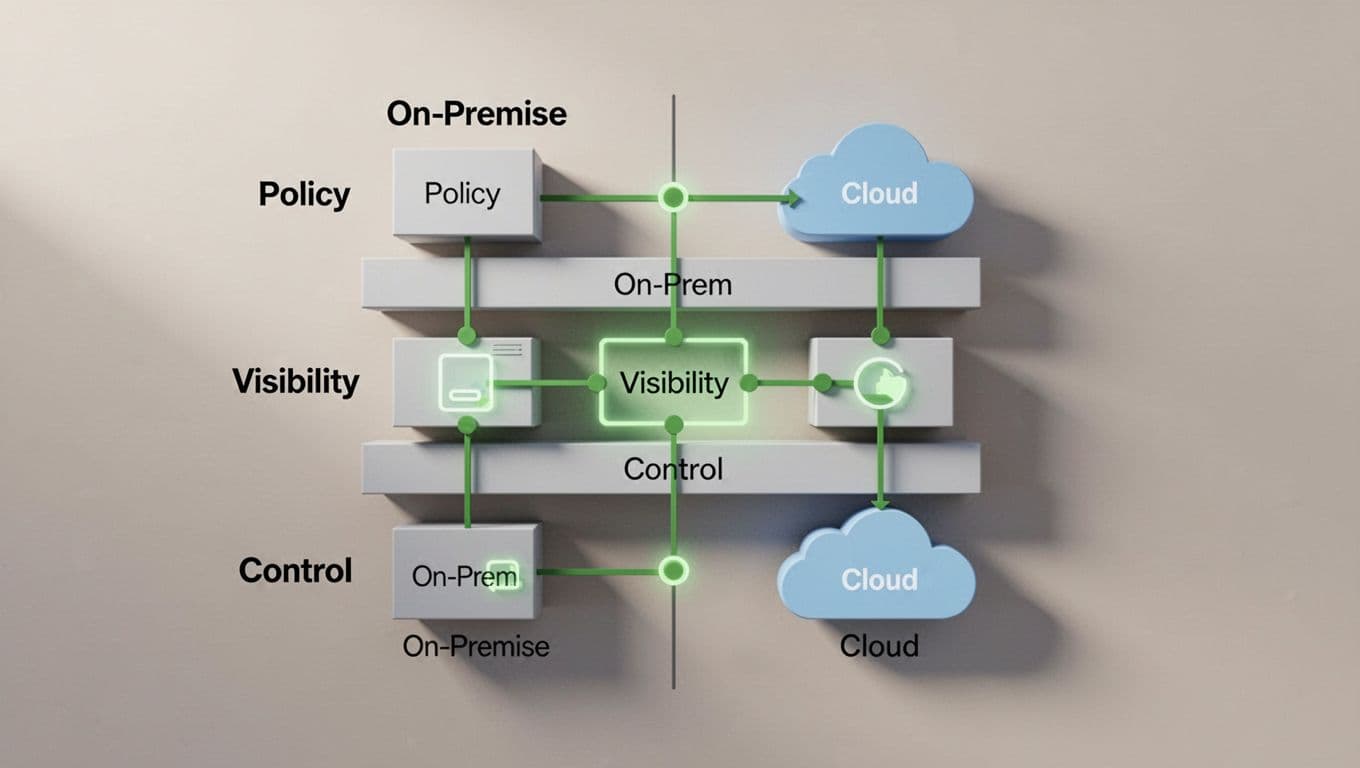
Hybrid differs from pure setups. On-premises uses static rules; cloud needs dynamic scans. Your framework unifies them. For example, CSPM spots misconfigs in AWS S3 buckets and on-prem shares alike.
Add AI for anomaly detection. It flags odd behavior faster than rules. Market trends show hybrid growing fastest in CSPM adoption.
Unify Policies, Visibility, and Controls
Bring it together with shared services. Central IAM directory handles users for all environments. Tools like Okta or Entra ID federate access.
For visibility, normalize logs. SIEM ingests from cloud APIs and on-prem agents. CNAPP covers workloads end-to-end.
Policies stay consistent via automation. IaC scans enforce baselines in Terraform deploys. IBM’s well-architected framework stresses this for hybrid compliance.
Controls automate remediation. SOAR tickets fix issues, like closing open ports. Zero-trust segments traffic; no flat networks.
Real-world risk: Privilege drift. A dev with cloud admin rights accesses on-prem via VPN. Unified IAM revokes it automatically.
DevSecOps shifts security left. Scan in CI/CD pipelines. This cuts drift.
Implementation Steps
Build your framework in phases. Assess first, then define, monitor, and automate.
Assess current posture. Map assets with CSPM. Identify gaps like unpatched servers or open buckets.
Define policies. Align on NIST or ISO 27001. Document IAM rules, encryption standards.
Set up monitoring. Deploy SIEM and CNAPP. Dashboards show risks in real time.
Automate controls. Use SOAR for responses. Test with red-team sims.
Use this checklist to gauge your setup:
- Do policies apply uniformly across on-prem and cloud?
- Is visibility full, with normalized logs?
- Does IAM enforce least privilege everywhere?
- Are controls automated, including zero-trust?
- Run weekly CSPM scans; fix high risks in 72 hours.
Test quarterly. Adjust for new threats. Chiefviews shares 2026 best practices like just-in-time access.
Scale with team training. DevSecOps roles bridge gaps.
Key Takeaways
Your hybrid cloud security posture framework unifies policy, visibility, and controls to close gaps that pure-cloud or on-prem miss. Focus on automation and zero-trust for 2026 threats.
Teams with strong setups cut breach risks sharply. Start assessing today.
Need expert help to hire architects or refine culture? Book a Discovery Call with Bud Consulting.
(Word count: 982)