table of contents
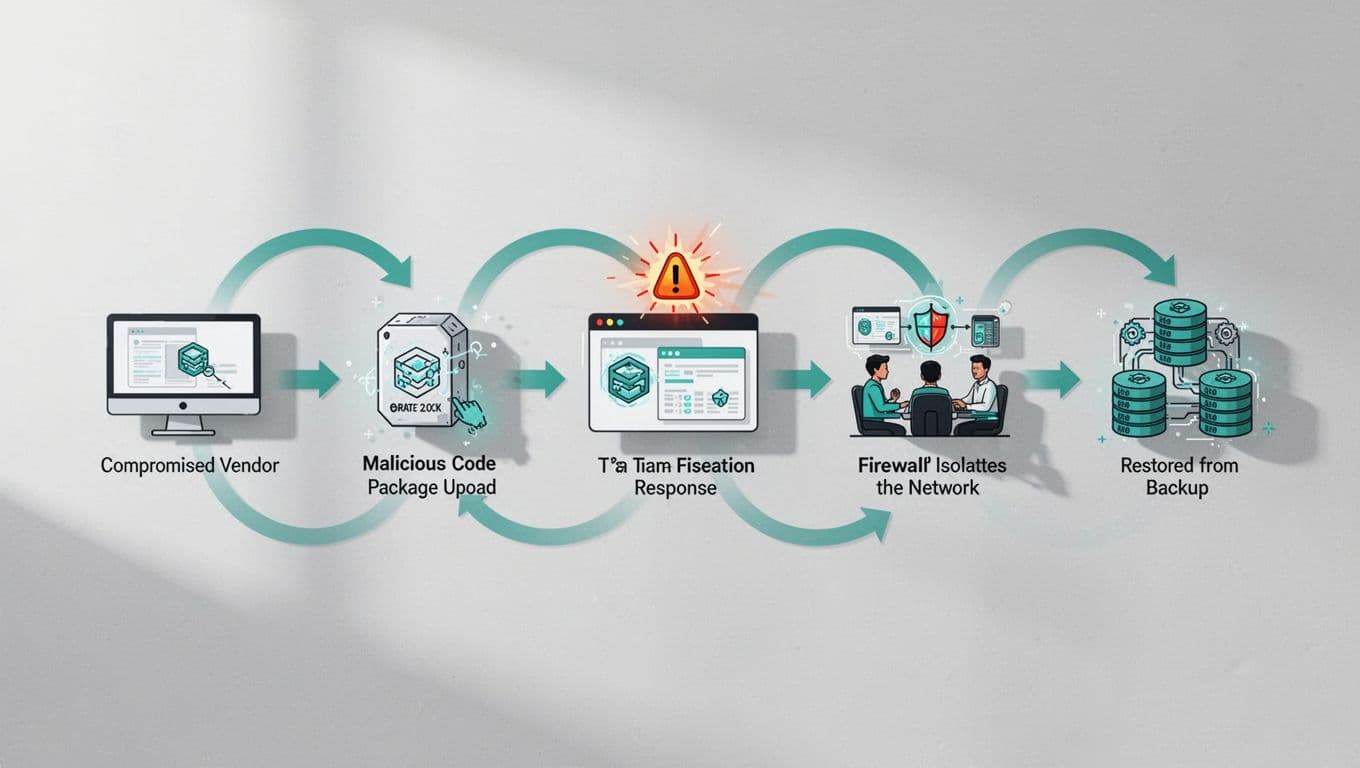
Supply chain attacks hit hard because they slip past your defenses through trusted vendors. Think of the recent TeamPCP compromise of Trivy in March 2026, where hackers swapped code tags and stole credentials across multiple tools. Or the Axios npm package tainted mid-April, downloaded half a million times before detection. These real events show why you need to practice responses now.
You handle incident response or third-party risks, so tabletop exercises let your team spot gaps without real damage. They build muscle memory for tough calls under pressure. This guide walks you through setup, scenarios, and tips so you run effective supply chain tabletop exercises.
Why Supply Chain Tabletop Exercises Matter Now
Organizations face rising threats from vendor compromises. In 2026, 47% of attacks start with stolen vendor credentials, per recent stats. Yet many teams lack clear playbooks for these scenarios.
Tabletop exercises test decisions, not tech. Participants discuss responses to simulated events, revealing coordination issues or policy holes. NIST CSF 2.0 stresses supply chain risk under its Govern function (GV.SC), urging regular drills.
Recent hits like ShinyHunters targeting Salesforce setups highlight misconfigurations in third-party access. Run these exercises quarterly to align SOC, IT, and execs. They expose blind spots in SBOM reviews or isolation steps.
Benefits stack up fast. Teams improve response times because they rehearse uncertainty. One exercise might uncover missing vendor contracts or weak IR handoffs.
Core Components for Effective Tabletop Drills
Start with clear objectives tied to your risks. Focus on software supply chains if you rely on open-source tools or CI/CD pipelines.
Gather 6-12 people: SOC analysts, IR leads, legal, procurement, and a CISO rep. Use roles like “vendor manager” or “network engineer” to simulate real flow.
Pick a neutral facilitator. They control pace and injects without biasing outcomes. Tools stay simple: printed scenario packets, timers, and flip charts.
Incorporate frameworks like NIST SP 800-84 for structure. It outlines discussion-based playbooks. For supply chain focus, weave in CISA’s tabletop exercise packages, which include vendor breach modules.
Prep data matters. Share org charts, IR plans, and sample SBOMs beforehand. This grounds talks in reality.
Building Your Scenario: A Sample Software Supply Chain Compromise
Craft a believable story based on trends. Your fictional vendor, CodeForge, builds a logging library your devs pull from npm weekly.
Scenario: CodeForge devs use weak credentials. Attackers (like TeamPCP style) hijack their repo March 20, 2026. They tag version 2.4.1 with malware that exfiltrates API keys on install.
Your pipeline grabs it April 1 during a build. Systems run the tainted code silently for days. Alerts flag odd outbound traffic April 15.
This mirrors Axios or Trivy attacks. It tests SBOM use for quick vuln mapping.

Discuss phases: detection via EDR, then triage. Does procurement have vendor SLAs? How fast can you rotate keys?
Tie to NIST CSF 2.0’s Identify (ID.SC) for supply chain mapping. Add twists like lateral movement to prod databases.
Crafting Realistic Injects
Injects drive action. Release them every 15-20 minutes to mimic escalation.
Base them on real tactics. Start subtle, build tension.
| Time | Inject | Team Discussion Prompt |
|---|---|---|
| 0 min | Vendor alert: CodeForge repo compromised, tainted v2.4.1. | Review your SBOM. Which apps use it? |
| 20 min | EDR flags beaconing from build servers. | Isolate segment? Notify vendor? |
| 40 min | Keys exfiltrated; ransom note appears. | Activate IR? Check backups? |
| 60 min | Lateral to CRM; customer data at risk. | Comms plan? Legal on disclosure? |
This sequence forces choices under fog. Use Sysdig’s best practices for SBOM contracts in prompts.
After each, pause for 10 minutes. Note decisions on a shared board.
Facilitator Tips to Drive Value
Stay neutral. Probe with “What if?” but avoid leading.
Time box strictly. Use a 90-minute core session, plus 30 for debrief.
Watch for silos. Push cross-team input, like legal on breach reporting.
Record hotwash notes: wins, gaps, action items. Assign owners immediately.
Rotate roles next time. Analysts play execs to build empathy.
Draw from NIST SP 1305 for C-SCRM outcomes. Test GV.SC subcategories.
Encourage discomfort. Uncertainty reveals true plans.
Checklist to Run Your Own Supply Chain Tabletop Exercise
Use this to launch yours.
- Define scope: Pick one chain (e.g., open-source deps).
- Map participants and roles.
- Build scenario and 4-6 injects.
- Distribute pre-reads 1 week out.
- Run 2-hour session; debrief 30 min.
- Assign fixes with deadlines.
Follow up in 30 days.

SBOM reviews and vendor attestations shine here.
Key Takeaways
Supply chain tabletop exercises sharpen your edge against vendor breaches. They turn plans into instincts, as seen in recent 2026 attacks.
Run one soon. Track actions to close gaps.
Need help scaling these? Book a Discovery Call with Bud Consulting for tailored IR planning.
(Word count: 982)