table of contents
Remote security hiring now attracts more than strong applicants. It also attracts impostors, proxy interviewers, and deepfake-assisted fraud. When the role touches systems, data, or privileged access, candidate identity verification needs to be part of the interview design, not an afterthought.
The good news is that you don’t need intrusive tactics to do it well. You need a clear process, consistent checks, and a candidate experience that feels professional from the first email to the final decision.
Start with application data, not a camera test
Identity checks work best when they begin before the interview starts. Compare the candidate’s application, resume, calendar invite, email address, and profile details for consistency. Small mismatches are not proof of fraud, but they can tell you where to look closer.
For security roles, pay attention to details that are hard to fake without prep. Job titles, work dates, certification history, location, and recent project claims should line up. If a candidate says they led IAM work for three years, their answers should hold up when you ask about scope, tools, and team size.
A secure scheduling platform also helps. It keeps interview links, times, and participant records in one place, which reduces confusion and makes it harder for an impostor to slip in through a forwarded invite. That matters in 2026, when remote interview fraud is becoming more polished, especially in high-value technical hiring.
You can also spot issues early with simple logistics. Ask the candidate to confirm their preferred name, time zone, and interview device in advance. Fraudsters often stumble on the practical details.
Use a live camera check with clear boundaries
A live camera check is one of the most direct ways to confirm that the person on screen is the person you expect. Keep it short. Explain the step before the interview so it never feels like a surprise.
If your policy and local law allow it, ask the candidate to show a government ID on camera and compare it with the application name. The goal is a quick match, not a full document review theater. For US employers, the Department of Justice guidance on I-9 software programs is a useful reminder to keep identity handling lawful, consistent, and limited to what the process needs.
A polished video feed is not proof. A repeatable process is.
Keep the check respectful. Tell candidates why you’re doing it, how long it takes, and who will see the information. That transparency improves trust and lowers drop-off.
Image placement matters less than the message here: the camera step should feel like a normal part of a professional process, not an interrogation. If a candidate refuses a basic identity check without a good reason, that is useful signal in itself. Still, document the refusal and move according to policy, not gut instinct.

Add role-specific checks that are hard to fake
Deepfakes can mimic a face, but they struggle with real context. That’s where role-specific questions help. Ask the candidate to explain a past security decision, walk through a live scenario, or describe tradeoffs they made under pressure.
For example, an IAM specialist should be able to talk through provisioning, access review, and exception handling without drifting into vague language. A DevSecOps leader should explain how they handled pipeline gates, secrets management, and incident response. A candidate who only memorized buzzwords often falls apart when the questions get specific.
A short live task can also help. Keep it fair and relevant. Ask for a whiteboard explanation, a threat-model walk-through, or a risk ranking exercise tied to the job. These checks do more than test skill. They also reveal whether the interview partner is thinking in real time or reading from a script.
One practical sign of proxy interviewing is unnatural consistency across answers. The story sounds polished, but the details stay shallow. If you move from resume claims to recent decisions to technical tradeoffs, the gaps usually show up fast. For more examples of how teams are handling this, deepfake interview detection methods are getting a lot of attention for good reason.
Document the workflow so it stays fair
Identity verification only works when everyone follows the same playbook. Write down the steps, who owns them, and what happens when something looks off. That protects the hiring team and the candidate.
A simple workflow can look like this:
- Confirm the application details before the interview.
- Use a secure interview link and verified calendar invite.
- Perform a brief live camera check at the start.
- Run one role-specific knowledge check.
- Record the result and any follow-up action in the hiring file.
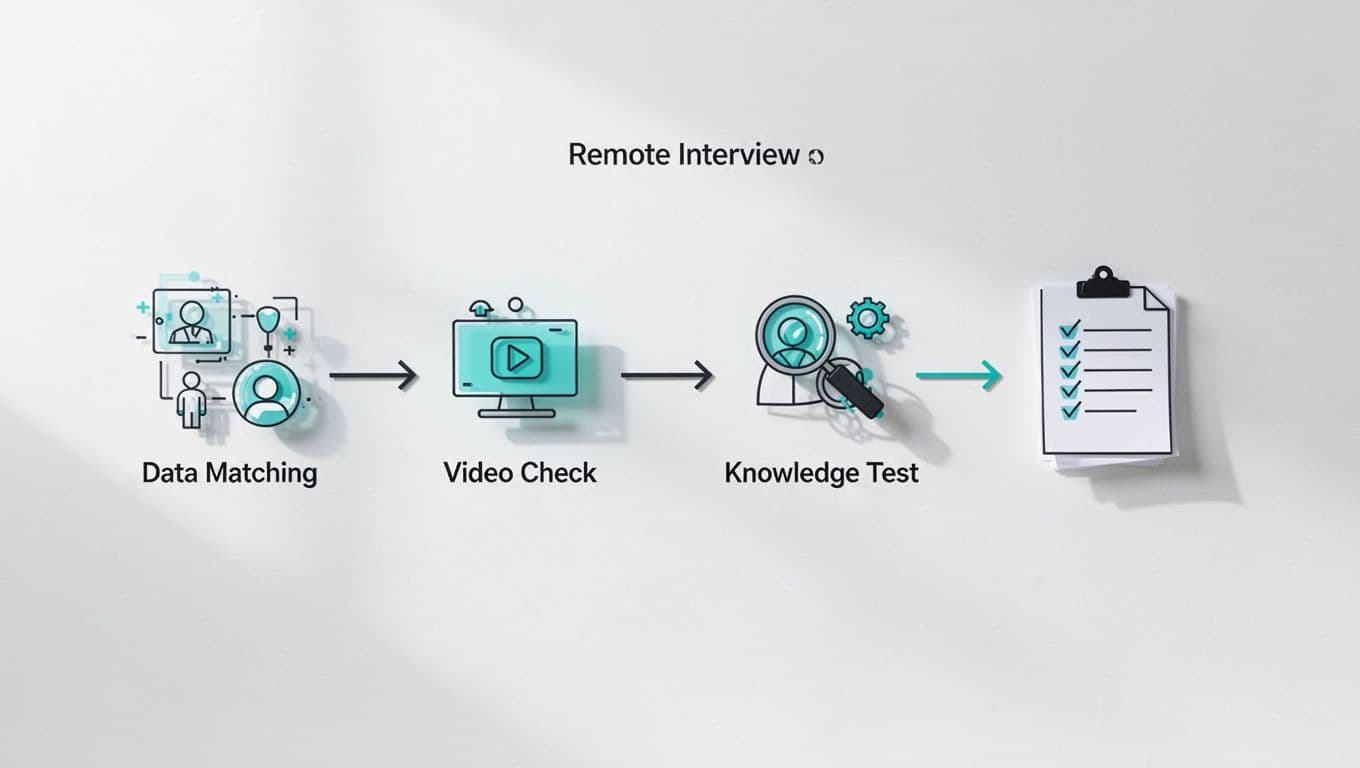
That structure makes reviews easier later. It also helps if legal, HR, or security asks why a candidate moved forward or stopped. Keep notes factual. Avoid subjective labels like “looked suspicious” unless you can tie them to a specific behavior.
Protect privacy and reduce bias
Good verification uses the least data needed to make a sound decision. You don’t need to collect extra documents, retain full ID numbers, or store sensitive files longer than policy allows. In most cases, a name match, live camera confirmation, and documented review are enough.
Bias can creep in when interviewers use the wrong signals. Accent, appearance, age, or background setting should never decide identity. Standardize the process so every candidate goes through the same steps. That keeps the focus on proof, not assumptions.
Tell candidates what you collect, why you collect it, and how long you keep it. If an accommodation is needed, offer one. A secure and respectful process usually gives you better cooperation than a rigid one.
If your team is hiring for senior security roles and wants a stronger interview workflow, Book a Discovery Call with Bud Consulting to talk through a practical approach.
Remote hiring fraud keeps getting smarter, but your response doesn’t need to get harsher. It needs to get clearer. When candidate identity verification is consistent, lawful, and respectful, you protect the role, the team, and the candidate experience at the same time.