table of contents
Hybrid estates expose more than most teams can track. One cloud app can depend on a SaaS login, an on-prem service, and an internet-facing API, so one missed control can open a longer path than expected.
That is why CTEM coverage matters. In hybrid environments, the goal is not to scan more often. It is to keep a live view of what exists, what can be reached, and what an attacker can do next. The checklist below keeps that scope practical.
What CTEM coverage means in a hybrid estate
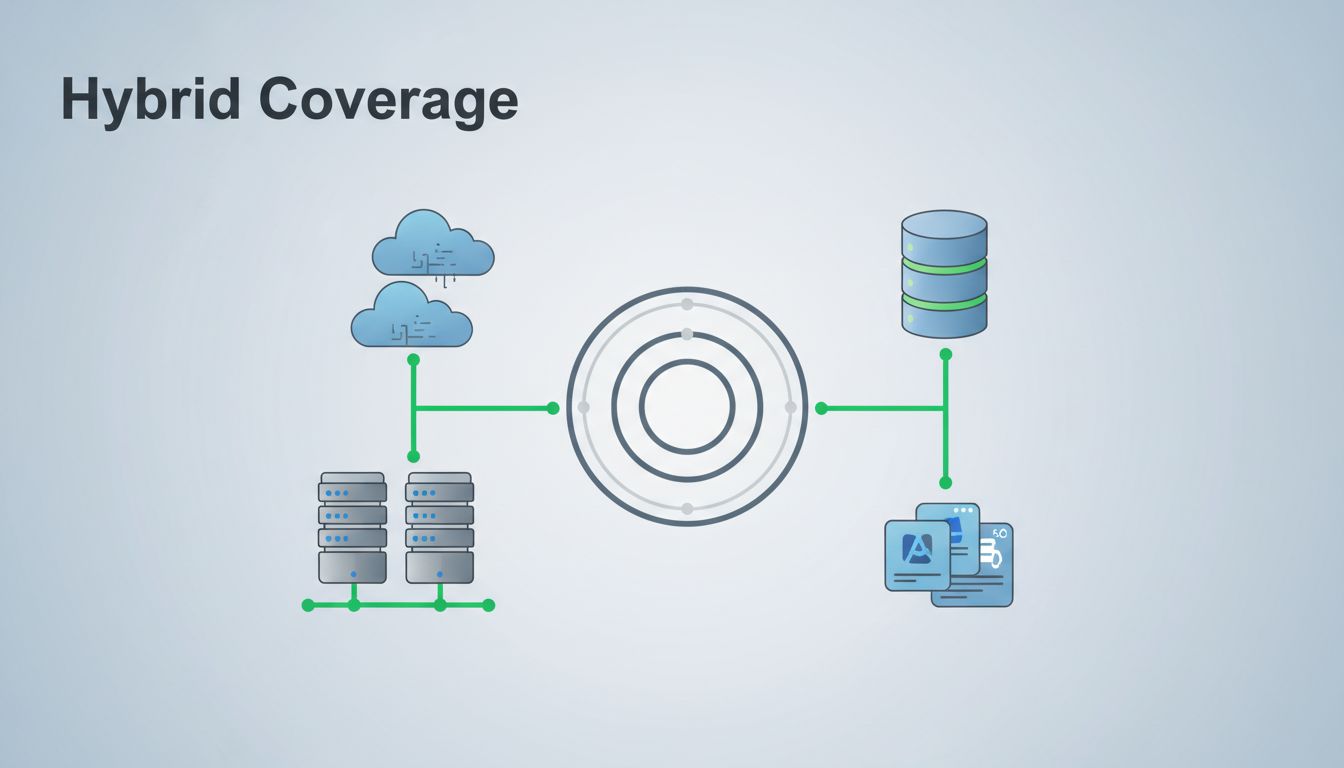
CTEM coverage starts with a simple idea, every exposed path matters, not every asset in the abstract. That means on-prem servers, cloud workloads, containers, SaaS apps, identities, external assets, and the connectors between them all belong in the same view.
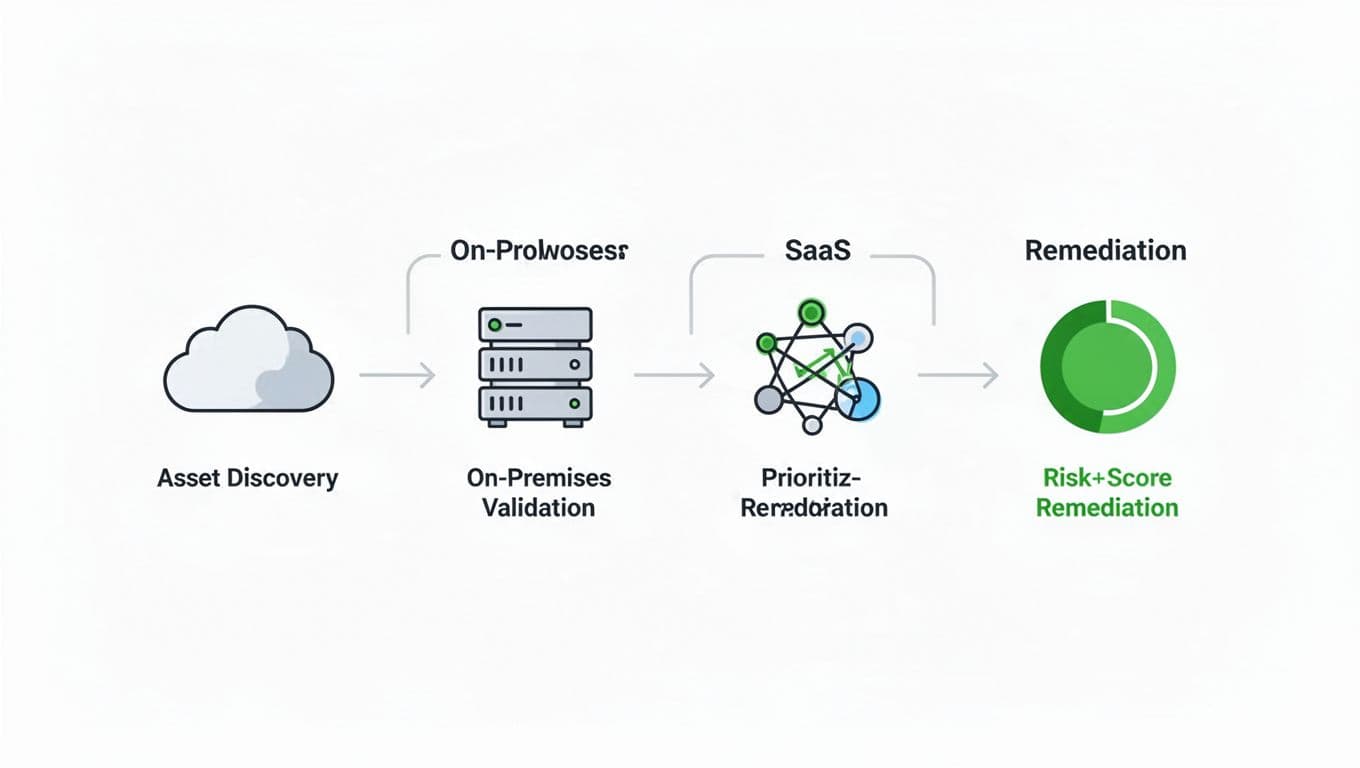
For a useful baseline, scope around business services first. A payroll system, a customer portal, or a patient app is easier to defend than a raw asset list. XM Cyber’s practical CTEM checklist follows that same logic, beginning with scoping before discovery and validation.
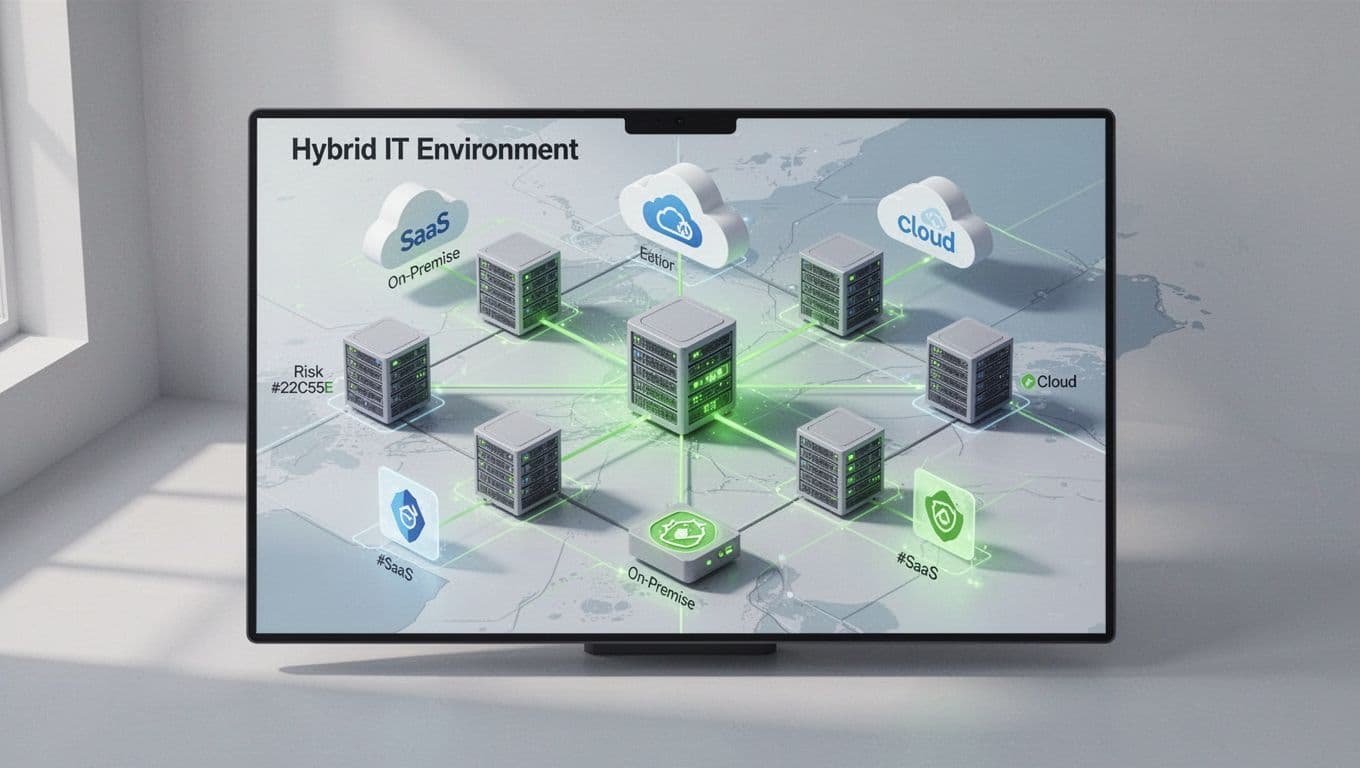
The best hybrid programs treat coverage as a living map. As assets change, the map changes too. If it doesn’t, the program is already behind.
The checklist security teams can run now
Use this order to keep the work focused and repeatable.
- Start with the business services that matter most. Tie each one to owners, data types, and acceptable downtime.
- Build one inventory across on-prem, cloud, SaaS, identities, APIs, and internet-facing assets. Separate lists leave gaps.
- Discover continuously, not on a quarter-end cycle. New accounts, new storage, and new SaaS tenants appear fast.
- Validate exposure paths, not just scan results. A weak password or stale admin role can matter more than a medium CVE.
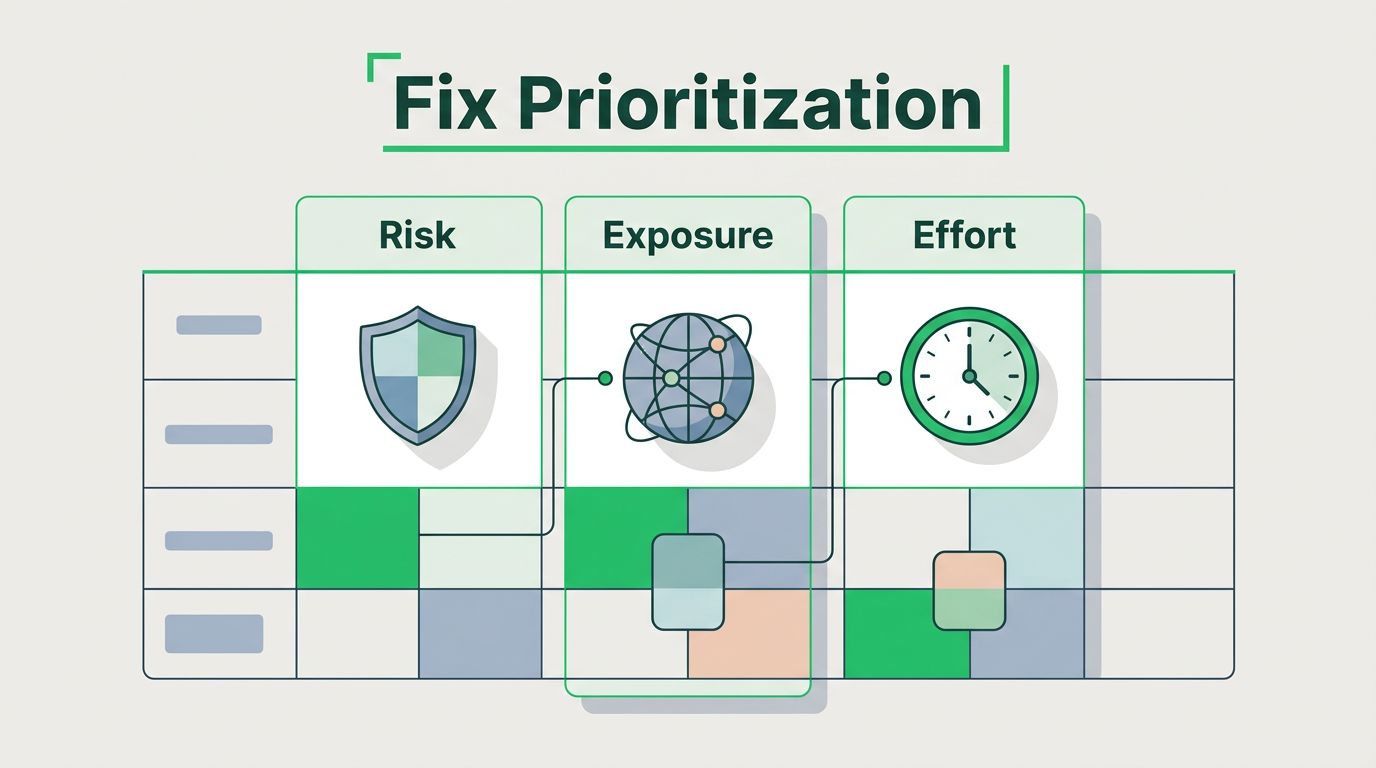
- Prioritize by attacker reach, privilege gained, and business impact. Severity scores alone hide real risk.
- Track remediation ownership. Every high-priority exposure needs one team, one deadline, and one verification step.
- Re-test after the fix. A closed ticket does not prove the path is gone.
A clear checklist also helps teams compare CTEM with older vulnerability programs. The difference is easy to miss until you put it side by side.
| Area | Vulnerability management | CTEM |
|---|---|---|
| Main focus | Known CVEs and patch status | Real exposure across attack paths |
| Coverage model | Inventoried systems | Hybrid estate, identities, SaaS, and external surface |
| Prioritization | Severity first | Business impact plus attacker reach |
| Output | Patch backlog | Measurable exposure reduction |
A useful comparison like CTEM vs vulnerability management vs exposure management makes the gap obvious. CTEM asks what an attacker can actually use, then focuses effort there.
If you cannot trace an exposure to a business service, it probably belongs lower on the list.
Where hybrid coverage usually breaks
Hybrid coverage fails at the seams. Identity data sits in one tool, cloud posture in another, and SaaS risk in a third. Meanwhile, the attack path crosses all of them.
That’s why CTEM programs need exposure validation, not just alerts. SANS’ guide on operationalizing CTEM within the SOC shows the value of sharing the same facts across detection, validation, and response. If the SOC sees one story and the exposure team sees another, prioritization slips.
In hybrid environments, watch these failure points first:
- stale identity owners after role changes
- shadow SaaS with weak admin controls
- cloud assets exposed through old security groups
- on-prem systems that still trust broad internal access
- missing links between ticketing, IAM, and cloud ops
These are small problems on paper. In a real attack path, they stack fast.
Make the program work across teams
Coverage only works when the right teams see the same exposure picture. Security can find the issue, but platform, cloud, app, and IAM teams usually need to fix it. Therefore, CTEM should feed ITSM tickets, CI/CD checks, cloud guardrails, and identity workflows.
Set one rule for each material exposure, who owns it, how fast it must be fixed, and how the fix gets verified. That keeps the work from drifting into a queue of unowned issues. It also helps leadership see progress in terms that matter, like reduced reachable paths and faster validation cycles.
When team gaps slow the program down, role coverage matters too. If you need help finding cloud security, IAM, DevSecOps, or offensive testing talent, Book a Discovery Call with Bud Consulting.

What strong CTEM coverage changes
Strong CTEM coverage gives you one current answer to three hard questions, what exists, what matters, and what an attacker can reach next. That is a much better use of time than chasing every alert in every system.
In a hybrid estate, coverage is the program. Everything else depends on it. If the map is current and the priorities are real, remediation gets faster and noise gets smaller.