table of contents
Your network just suffered a breach. Attackers slipped through, and now you need answers fast. A network forensics expert can trace the traffic, spot the entry point, and build a case for recovery or court.
These pros differ from general cybersecurity teams. They focus on live network data, not just prevention. Digital forensics experts handle disks and devices; network specialists chase volatile packets that vanish without captures. In 2026, with cloud shifts and AI threats rising, hiring one right saves time and money.
This guide walks you through the process. You’ll learn what to seek, where to look, and how to vet candidates.
Why You Need a Network Forensics Specialist Now
Breaches hit harder each year. Remote work and cloud services make traffic complex. Traditional cybersecurity stops threats upfront. Network forensics kicks in after: it reconstructs attacks from packet captures and logs.
Consider a ransomware case. General IT spots the alert. A network forensics pro dives into Wireshark traces. They reveal command-and-control channels or data exfiltration. This sets it apart from disk-based digital forensics, where evidence sits static. Network data is fleeting, so pros use tools like intrusion detection systems from the start, as noted on Wikipedia’s network forensics page.
In 2026, demand surges. Over 500,000 cybersecurity jobs open in the US, with DFIR roles like network forensics growing fast. AI automates basic analysis, but humans handle nuanced threats like encrypted tunnels. Banks and healthcare firms hire internals; smaller teams bring in consultants.
You might need one for incident response, compliance audits, or litigation. Proactive scans spot risks too. Skip this hire, and you risk fines or repeated hits.
Key Skills and Qualifications to Look For
Top candidates master packet analysis. They dissect traffic with Wireshark or tcpdump. Look for experience in full packet captures, not just alerts.
Core skills include:
- Tracing lateral movement in hybrid clouds.
- Rebuilding sessions from encrypted flows.
- Volatility handling in AWS or Azure environments.
Certifications matter. GIAC Network Forensic Analyst (GNFA) proves advanced skills in logs and metadata. GCFA covers incident response depth. CHFI suits entry levels, but pair it with real cases.
Experience trumps paper. Ask for past breaches: “Walk me through a DNS tunneling hunt.” In 2026, expect AI tool familiarity. Pros use machine learning for anomaly detection, per recent network forensics market reports.

Background checks reveal court testimony. Legal cases demand chain-of-custody proof. Remote forensics pros shine here; no travel for evidence grabs.
Test knowledge early. Can they explain QUIC protocol risks? Or zero-day exploits in IoT traffic?
Where to Source Your Network Forensics Expert
Start with niche platforms. LinkedIn works for broad searches, but filter by “network forensics” and GNFA. Groups like SANS Institute connect you to pros.
Specialized sites speed things up. Upwork lists freelancers with DFIR portfolios. For vetted talent, check firms offering packet analysis experts. Smartbrain.io screens Wireshark specialists via quizzes and real tasks.
Conferences matter. Black Hat or SANS summits in 2026 draw experts. Post jobs on Indeed with “cloud network forensics” to tap 1,000+ DFIR openings.
Internal options exist. Train a SOC analyst, but that’s slow. Outside consultants fill gaps quick, especially for one-off probes.
Networks like ISC2 chapters yield referrals. Avoid generalists; seek those with 5+ years in traffic reconstruction.
Screen Resumes and Run Initial Tests
Job posts attract hundreds. Narrow fast. Require GNFA or equivalent, plus 3-5 breach case studies.
Scan for red flags: No packet tool mentions? Pass. Vague “cybersecurity” claims without network focus? Next.
Phone screens last 15 minutes. Ask: “How do you capture traffic in a zero-trust setup?” Good answers reference Zeek or Suricata.
Technical tests seal it. Send anonymized pcaps. Time them on finding exfil. Tools like CyberForensics.com’s expert guide suggest CHFI checks too.
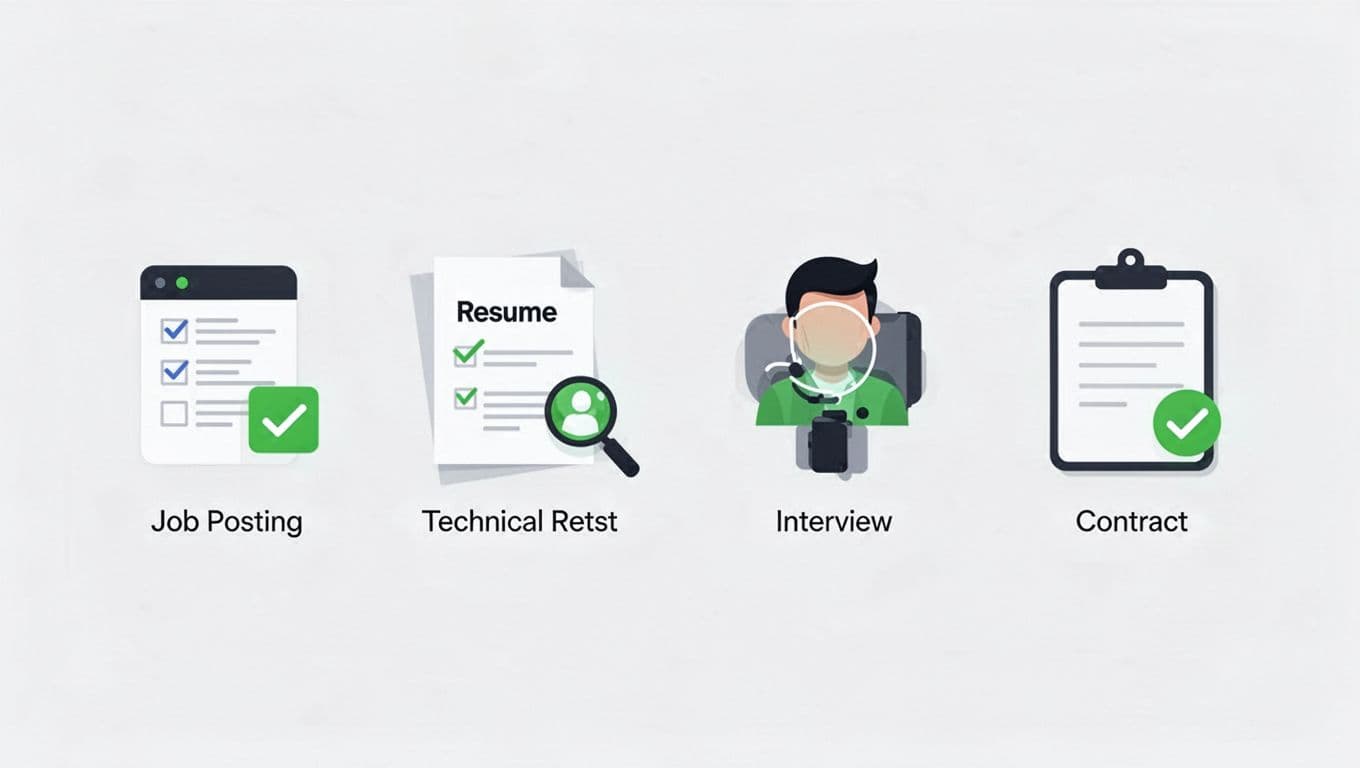
Interviews probe depth. Scenario: “Encrypted C2 in RDP traffic. Your steps?” Expect volatility plans and evidence preservation.
Reference calls confirm. Past clients verify testimony quality.
Set Rates and Negotiate Contracts
Freelancers charge $150-300/hour. Full-timers hit $150K+ base. Factor 2026 trends: Cloud skills add 20%.
Fixed-fee probes cost less for scopes. Daily rates suit ongoing hunts.
Contracts cover NDAs, data handling, and deliverables. Specify remote access rules.
Trial days test fit. Pay for a mock investigation.
Final Checklist Before You Sign
Pause before ink. Verify these items to avoid pitfalls.
- Certifications current? Check GNFA or GCFA expiration.
- Case portfolio? Review three redacted reports.
- Tools match your stack? Confirm Wireshark, ELK, cloud forensics.
- Legal experience? Ask for deposition examples.
- References vetted? Call two recent clients.
- Rates and scope aligned? No vague “T&M” without caps.
- Insurance proof? Cyber liability coverage.
- Exit clause? Clear data return process.

This list protects you. One miss leads to evidence issues.
If sourcing proves tough, Book a Discovery Call with Bud Consulting. They specialize in DFIR talent.
Key Takeaways
Hiring a network forensics expert boils down to skills, proof, and fit. Focus on packet pros with 2026-ready tools like AI anomaly detectors and cloud captures. Vet through tests and cases, not resumes alone.
You now have a clear path. Act soon; threats wait for no one. Your next hire turns breaches into wins.