table of contents
Your security team spots threats daily. But do they catch everything a real attacker might try? In 2026, breaches hit through cloud identities and supply chains more than ever. An in-house red team fixes that gap. It runs ongoing attack simulations tailored to your setup.
External hires help with one-off tests. Internal teams deliver constant pressure and deep knowledge. They turn findings into fixes fast. This guide walks you through a practical path. You’ll see how to start, scale, and measure results.
Assess Your Current Security Posture First
Start with a clear picture of risks. What attacks fit your industry? Financial firms face credential theft. Retail deals with ransomware via vendors.
Map your environment. Note cloud sprawl in AWS or Azure. Check hybrid setups with on-prem servers. In 2026, 71% of teams lack full visibility here. Attackers hide in those gaps.
Run a quick gap analysis. List high-value assets like customer data or IP. Ask: Can someone pivot from email to admin access? Use frameworks like MITRE ATT&CK for this.
Tools like BAS platforms automate basic checks. They mimic attacks non-stop. Pair them with manual tests later. This baseline shows if you’re ready for red teaming.
Your CISO needs buy-in early. Share breach stats from 2025. Self-detection rose to 46% for proactive teams. Position your red team as the tool for that edge.
Decide: In-House Red Team or Outsource?
Many leaders debate this. Outsourcing costs $50K to $150K per engagement. It’s quick for starters. No hiring hassle. Firms bring fresh tactics from other clients.
In-house builds ownership. You control cadence. Teams learn your systems deeply. Retention costs add up, though. Expect $150K to $250K per operator, plus tools.
Hybrid wins most cases. Use outsiders for quarterly deep dives. Internal staff handles daily emulations. For 8-12 tests a year, in-house pays off.
Here’s a quick comparison:
| Factor | In-House Red Team | Outsourcing |
|---|---|---|
| Cost per year | $500K+ for 3-person team | $200K-$600K for 4 engagements |
| Knowledge depth | High, custom to your environment | Broad but generic |
| Speed to start | 3-6 months | Immediate |
| Scalability | Grows with hires | Limited by contracts |
Pick based on volume. Frequent needs favor internal. For details on tradeoffs, check PINE’s analysis on in-house vs. outsourced red teaming. It matches 2026 realities.
Assemble the Right Team Structure
You need 3-5 people for a starter team. A lead plans ops. Operators run simulations. Analysts track detections.
Hire from offensive backgrounds. Military or pentest pros know real tactics. Train on cloud identity attacks. These hit hard now.
Include a purple team role. They bridge to defenders. This setup runs joint exercises. It speeds fixes.

Lead reports to you or SOC head. Keep them separate from blue teams. This avoids bias. Budget for certs like OSCP. Refresh skills yearly.
Scale later. Add AI specialists for prompt tests. Start small. Focus on quality hires.
Bud Consulting helps find these roles. They specialize in offensive security talent.
Choose Tools and Safe Infrastructure
Red teams need isolated setups. Use AWS or GCP for C2 servers. Keep them external to your prod.
Core tools: Cobalt Strike for ops. BloodHound maps identities. Custom scripts for cloud jumps.
BAS tools like Atomic Red Team run free emulations. They scale tests across endpoints.
Set safety rules. Define scopes. Use kill switches. Get legal sign-off first.
In 2026, AI aids here. It generates variants fast. Still, humans craft custom paths.
Budget $50K yearly. Open-source cuts costs. Test tools in a lab first.
Integrate Purple Teaming Practices
Purple teaming pairs reds and blues. Reds attack. Blues detect. They debrief together.
This beats solo reports. Blues tune rules live. Fixes happen in days, not months.
Run weekly sessions. Start with identity tests. Simulate helpdesk tricks. Track blue response times.
BAS complements this. It runs 24/7 baselines. Purple adds human creativity.

In 2026 trends, purple dominates. It builds SOC skills. Regs like NIST push it for proof.
Document lessons. Feed into playbooks. This creates a feedback loop.
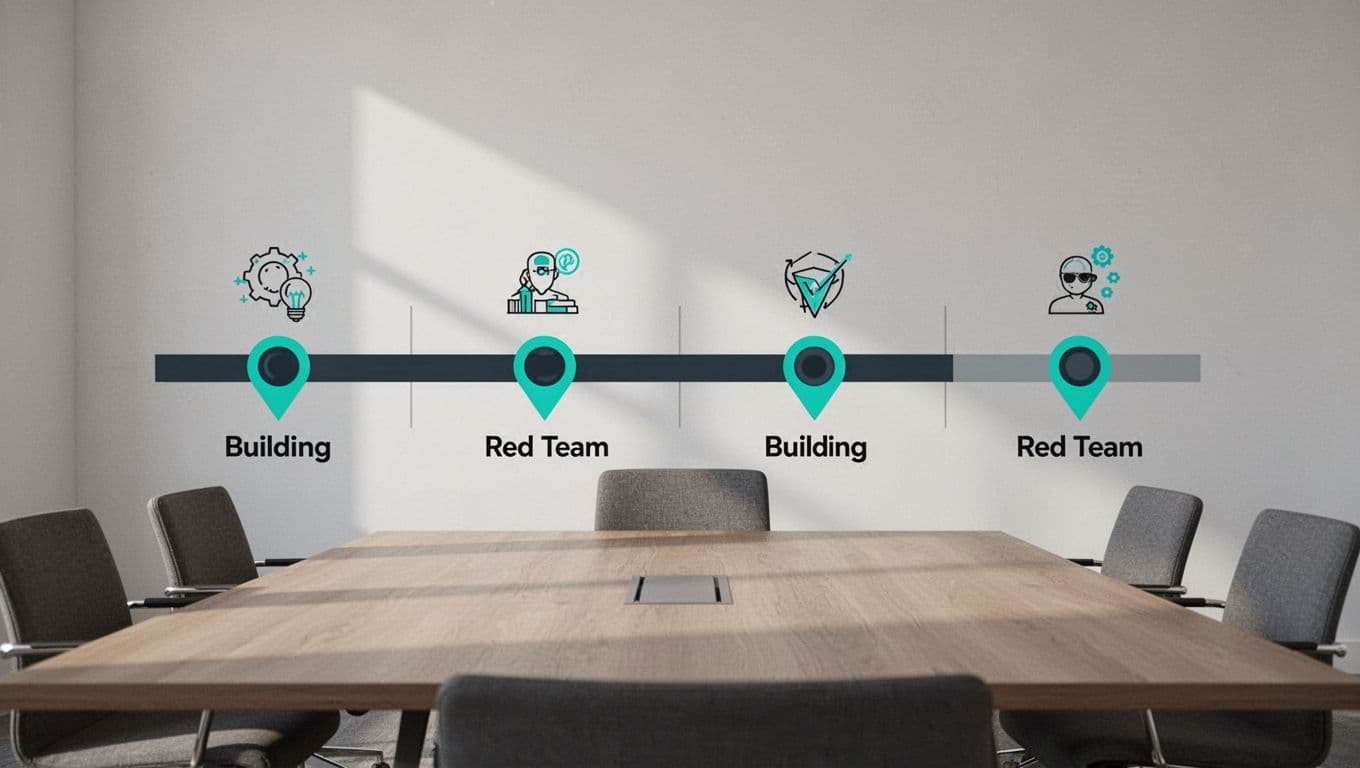
Follow a Phased 12-24 Month Roadmap
Build in stages. Avoid big bangs.
Months 1-3: Plan and hire. Assess posture. Get budget. Hire lead and one operator.
Months 4-9: Build skills. Set up labs. Run internal emulations. Start purple sessions.
Months 10-18: Execute full ops. Hit cloud and hybrid paths. Measure baselines.
Months 19-24: Mature. Automate with AI. Integrate compliance tests. Scale team.
For a full framework, see Tactical Adversary’s internal red team phases. It outlines crawling to flying stages.
Adjust for your size. Track milestones quarterly.
Measure Success with KPIs
Numbers prove value. Boards want business impact.
Key metrics:
| KPI | Target (Mature Team) | Why It Matters |
|---|---|---|
| Detection Time (MTTD) | Under 30 minutes | Shows SOC speed |
| Findings Fixed Rate | 90% within 30 days | Tracks remediation |
| Coverage Rate | 80% of assets | Ensures broad testing |
| Critical Findings/Quarter | 5-10 | Flags real risks |

Use dashboards. Tools like Splunk visualize trends. Compare to benchmarks from redteams.ai metrics guide.
Tie to ROI. Faster detection saves millions in breaches.
Handle Ethics, Safety, and Compliance
Ethics first. Always get written rules of engagement. No production disruptions.
Legal reviews scopes. Cover data handling. In 2026, regs demand proof of resilience.
Safety controls: Staging environments. Canary tokens alert on escapes.
Train on boundaries. Debriefs reinforce them.
Compliance links red team to audits. Test NIST or OWASP paths. Document for regulators.
Conclusion
An in-house red team shifts you from reactive to ahead. It exposes cloud identity gaps and builds purple skills. Follow the phases. Track KPIs like detection time.
Start small. Measure wins. Scale with hybrid support. Your defenses strengthen fast.
Ready to hire? Book a Discovery Call with Bud Consulting for talent advice.