table of contents
Managing security across fragmented cloud environments often feels like trying to hold back the tide with a sieve. Most organizations today juggle resources across AWS, Azure, Google Cloud, and countless SaaS applications, creating a sprawling surface that traditional perimeter defenses cannot protect. To address these gaps, you need a strategy that assumes breach and validates every connection, regardless of where the traffic originates.
Moving toward a zero trust multi-cloud architecture is less about replacing your existing tech stack and more about tightening how those pieces talk to each other. It requires shifting your mindset from trusting internal networks to verifying every identity and device request. If you are ready to modernize your security posture, you can Book a Discovery Call with Bud Consulting to start mapping your path forward.
Building a Foundation for Secure Multi-Cloud Access
Your first step is mapping your current assets. You cannot protect what you do not see, and visibility is often the biggest hurdle in multi-cloud environments. Different providers offer their own logging, monitoring, and alerting tools, such as AWS CloudTrail or Azure Monitor, which rarely speak the same language. This fragmentation leads to blind spots that attackers love to exploit.
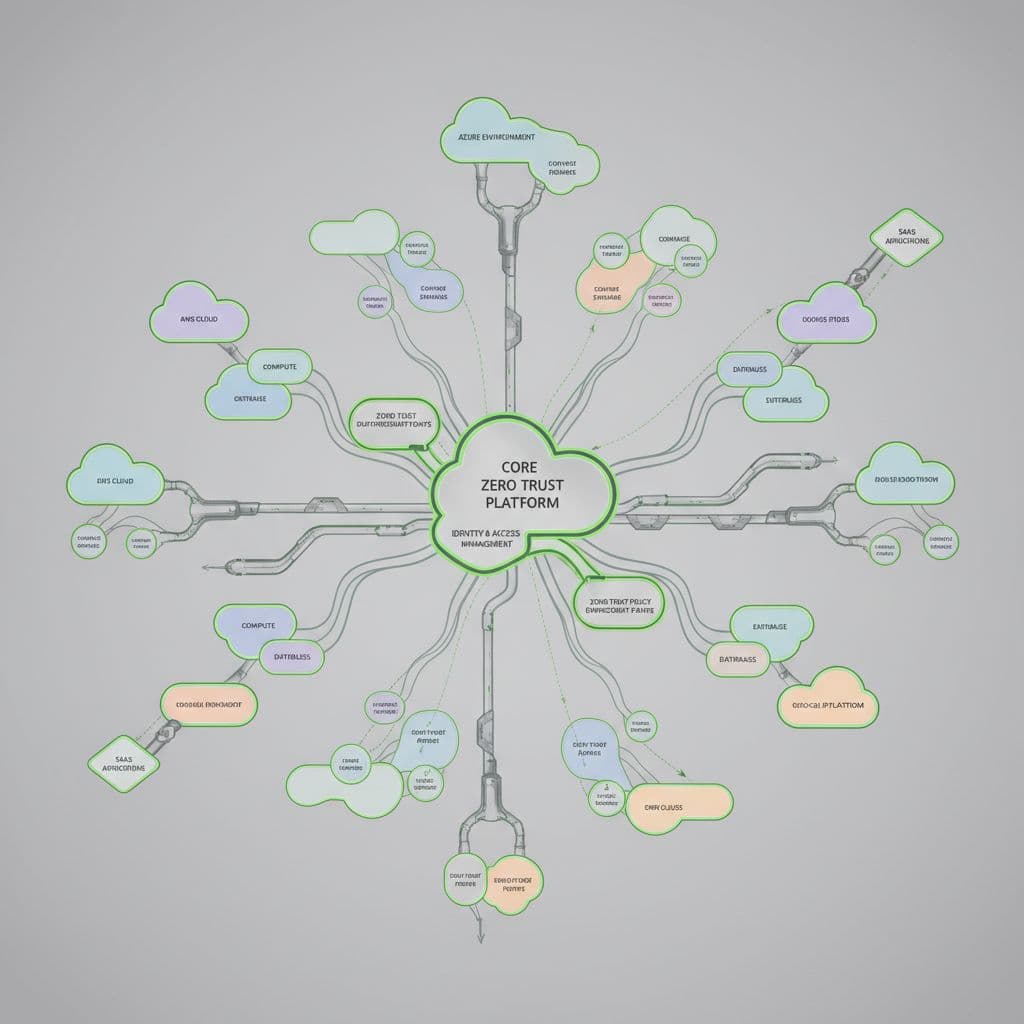
Standardizing your view across platforms is the foundation of a successful strategy. Many teams find that implementing zero trust in multi-cloud environments requires a unified control plane. You need tools that aggregate logs and telemetry into a single security operations center. Without this, your security team remains reactive, chasing alerts in isolated silos rather than addressing systemic risk.
Focus your initial efforts on identity. In a cloud-native setup, the identity is your new perimeter. If an attacker compromises a cloud service account with broad permissions, they don’t need to break through a firewall; they are already inside. Centralizing identity management across your cloud providers is not just a best practice, but a necessity for verifying access requests consistently.
Core Principles for Identity-Centric Security
Once you have visibility, you must apply the principle of least privilege. This means granting only the minimum access necessary for a user or service to perform a specific task, and only for the time they need it. It sounds straightforward, yet it is notoriously difficult to maintain as your cloud footprint grows.

Policies often become overly permissive over time because developers fear breaking applications. When planning how to implement zero trust, focus on automating these permissions. Use just-in-time access, which provides elevated privileges for a limited window, significantly reducing the blast radius of a compromised account.
Interoperability also remains a massive technical challenge. Because AWS, Azure, and Google Cloud use different IAM models, you might face policy silos where security rules enforced in one environment do not apply to another. To bridge the gap in zero trust operations, prioritize infrastructure-as-code. Defining your policies in code allows you to deploy the same security guardrails across multiple clouds automatically.
Phased Adoption and Maturity Models
Do not attempt a total overhaul of your security architecture overnight. A successful roadmap is iterative and prioritizes quick wins before moving to complex, automated controls. Start by securing your most sensitive data and high-risk applications. Once you prove the model works for your core business assets, you can scale it outward to lower-tier workloads.
Phase one should focus on basic hygiene. This includes enforcing multi-factor authentication (MFA) everywhere, hardening your root accounts, and rotating credentials regularly. You can also start tagging assets by risk level to inform future access policies. This provides immediate value and establishes the baseline required for more advanced automation later.
In the second phase, you move to continuous verification. This is where you connect your identity provider to your cloud environments for real-time access checks. Instead of checking credentials once at the login screen, your system validates the context of every request. Is the user on a managed device? Is the location unusual? Is the request coming at an odd hour?
Phase three involves full orchestration. This is the mature state where security policy is enforced through code across your entire estate. You utilize cloud-native application protection platforms (CNAPP) to monitor for misconfigurations and vulnerabilities across your cloud-native stack. At this point, your security team spends less time reviewing logs and more time fine-tuning the automation that keeps the environment secure.
Overcoming Common Implementation Pitfalls
One of the most common mistakes is treating security as a purely technical problem. If you force strict zero trust controls onto a development team without providing an easy way to request access, they will find ways to bypass your security. You must ensure that your security measures are friction-free enough that they do not block business operations.
Another pitfall is the assumption that a single tool will solve everything. Many vendors promise a “single pane of glass” that manages your entire multi-cloud security strategy, but these tools often fail to account for the unique quirks of each provider’s API. Always look for tools that support open standards and can integrate with your existing CI/CD pipelines.
Lack of buy-in from engineering teams often stunts progress. When developers view security as an obstacle, they prioritize speed over compliance. You must engage them early in the process and show them how automated security guardrails actually help them deploy faster and with more confidence. Make security a shared responsibility rather than something that happens after the code is written.
Metrics and KPIs for Measuring Progress
Measuring your progress ensures that your strategy remains on track. Without clear benchmarks, it is impossible to know if your investments are actually reducing risk or just adding complexity to your stack. Focus on metrics that reflect the health of your identity lifecycle, the effectiveness of your access controls, and the speed of your incident response.

The following table summarizes key areas you should track to monitor your zero trust health:
| Metric Category | Key KPI | Goal |
|---|---|---|
| Access Control | MFA Adoption Rate | Achieve 100% across all user roles |
| Identity | Just-in-Time Access Usage | Increase for all administrative tasks |
| Detection | Mean Time to Detect (MTTD) | Lower through automated alerting |
| Response | Mean Time to Respond (MTTR) | Decrease by automating policy enforcement |
| Compliance | Audit Findings Reduction | Lower the volume of open access violations |
Use these metrics to hold yourself accountable. If you notice a high authentication failure rate, it might indicate that your policies are too rigid, or that users are struggling with new tools. Use this data to adjust your approach, keeping the user experience in mind. Regular reporting also helps you justify additional budget or headcount to leadership by showing clear, measurable risk reduction.
Final Thoughts
Building a zero trust multi-cloud program is a multi-year journey. It is easy to get overwhelmed by the sheer number of moving parts, but you can succeed by focusing on one identity, one workload, and one cloud at a time. The goal is to build a system where trust is never assumed and every request is constantly verified.
Start by fixing your visibility gaps and centralizing your identity management. Once you have a firm grip on those two areas, you can layer on the automation and granular access controls that make the model truly effective. If you need help identifying your biggest risks or planning your next steps, we are here to support your team.
You have the tools and the framework to move forward. Your focus should remain on consistent execution and adapting your strategy to the realities of your specific cloud environment. Keep your security policies simple enough to manage, but rigorous enough to protect your most sensitive business data.





