table of contents
Contractors often get the same security course as employees, then miss the rules that matter most. That gap creates weak spots in access, data handling, and incident reporting.
Strong contractor security training ties the lesson to the role, the systems, and the data. It also covers what happens when the work ends, because contractor risk does not end with the last invoice.
The best programs read like a map, not a lecture. They show each contractor what they can touch, what they must protect, and what they must report.
Why contractor training needs its own rules
Contractors usually work under tighter timelines and broader risk. Many use their own laptops, remote networks, or shared workspaces. Others enter sensitive areas for a short project, which means they can miss local rules if training is too generic.
That is why third-party risk has to shape the lesson. Openforce’s guidance on independent contractor cybersecurity is a useful reminder that access, devices, and networks all matter. Federal programs take the same approach. DHS publishes security and training requirements for contractors, while CMS uses role-based training for people with security or privacy duties.
If a contractor does not need a resource, don’t train for it and don’t grant it.
The lesson should stay simple, because simple rules get used. Focus on least privilege, confidential data, phishing, and where to report trouble fast.
Write to the role, not the calendar
A developer needs different examples than a field vendor or a finance consultant. A contractor who handles source code needs to protect secrets, approve access requests, and avoid public code sharing. Someone who enters client sites needs badge rules, visitor escort rules, and clean-desk habits.
Use the role as the unit of design. Microsoft’s role-based access control guidance is a good reference point, because training should match the same access logic. Map each role to three things, the data it can touch, the systems it can use, and the risks it creates.
Every role should also include confidentiality obligations in plain language. Avoid legal copy that people skim past. Say what must stay private, where files can live, and which tools are approved.
That keeps the lesson short and focused. It also makes audits easier, because you can show why each topic exists.
Use a step-by-step framework that stays practical
A good training plan starts with the work, then moves to the lesson. This five-step outline keeps the content tied to risk.
- List contractor types and their access. Start with the project, the systems, and the data each role needs.
- Mark the highest risks. Note device use, remote access, physical entry, file sharing, and any regulated data.
- Assign one clear lesson to each risk. Keep it tied to phishing, data handling, badge use, secure storage, or reporting.
- Write actions, not policy language. Tell people how to verify a request, where to save files, and who to call first.
- Set completion and exit rules. Add owner approval, refresh timing, and a clean offboarding step for every contractor.
If a lesson does not change behavior, cut it. Short modules win because they are easier to remember under pressure.
A sample matrix for common contractor types
A matrix helps security, HR, and project owners stay aligned. It also shows where the same topic needs different depth.
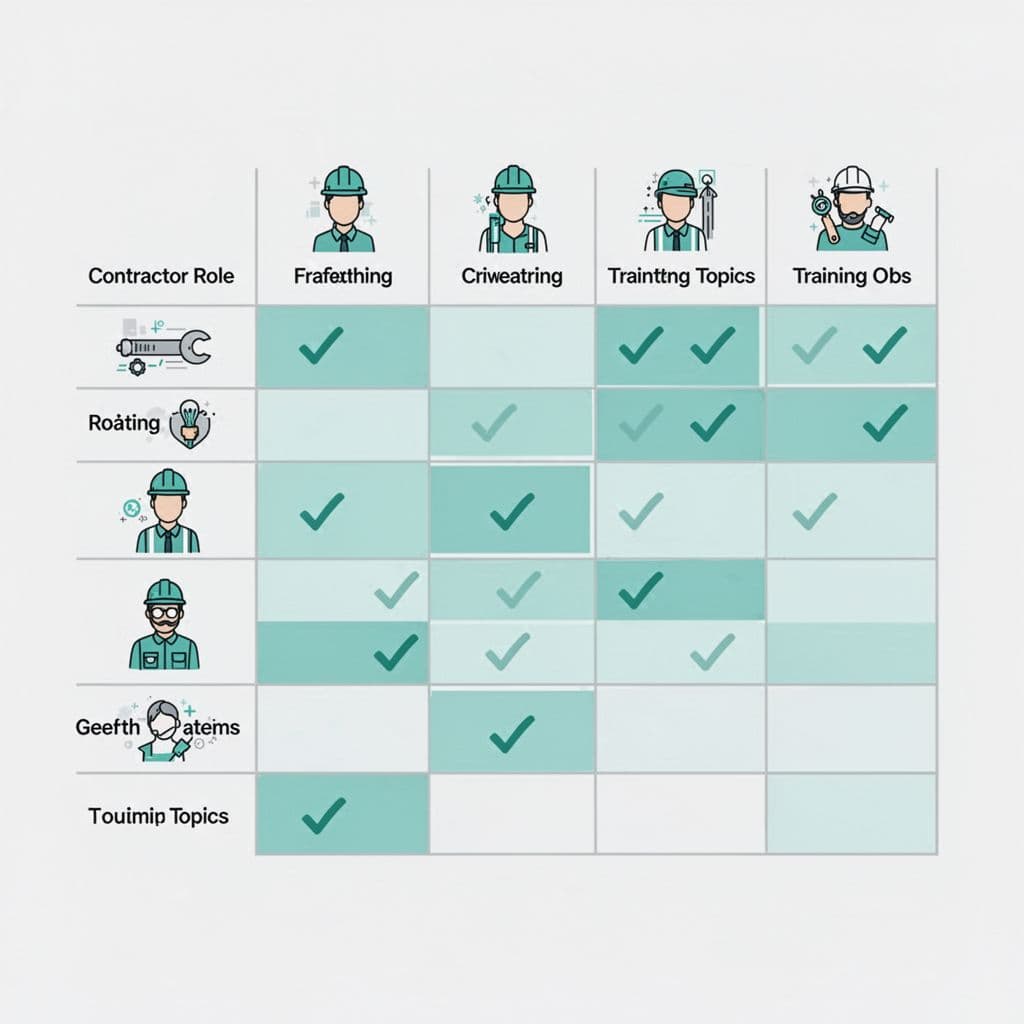
For a broader view of vendor education, third-party security awareness can help shape the content.
| Contractor type | Access they may need | Core training topics | Offboarding focus |
|---|---|---|---|
| Developer | Source code, test data, repo tools | Phishing, secrets handling, approved tools, data masking | Revoke keys, tokens, and repo access |
| IT admin or IAM contractor | Admin consoles, privileged accounts | MFA, least privilege, session logging, alert reporting | Remove elevated rights and rotate secrets |
| Consultant or analyst | Reports, client files, shared drives | Confidentiality, secure sharing, data classification, file retention | Delete local copies and confirm file return |
| Facilities or field vendor | Physical sites, badges, visitor areas | Badge use, escort rules, clean desk habits, device hygiene | Collect badges, keys, and site access |
The pattern is clear. Higher access means more detail around control, proof, and reporting. Lower access still needs training, but the focus shifts to physical security and data handling.
Make reporting and offboarding part of the lesson
Contractors need a fast, plain reporting path. Tell them what counts as an incident, lost devices, phishing clicks, strange login prompts, bad file shares, or a visitor issue. Then name the contact, the backup contact, and the expected response path.
Device and security hygiene belong here too. Contractors should know how to use approved devices, update software, lock screens, store files safely, and keep work separate from personal accounts. If they use a BYOD model, spell out the extra rules before access starts.
Access offboarding belongs in the training from day one. Make it clear that badges, VPN access, tokens, shared folders, and local copies must be returned or removed when work ends. If you need help turning policy into role-based modules and onboarding checklists, Book a Discovery Call with Bud Consulting.
Contractor training works when it matches the work
Contractors do not need more slides. They need training that matches the job, the access, and the exit plan.
When you build around least privilege, clear reporting, and clean offboarding, contractor security training becomes a real control. That is how you reduce third-party risk without burying people in policy.